Rescuing and restoring data
Lifebuoy

Armed with just standard Linux tools, users can recover files, resurrect partitions, and rescue damaged media.
Just imagine a good friend coming back from vacation totally downcast: Iceland was a total failure, she says – bad weather, lousy hotel, and her camera ate up its memory card. All the geysers and trolls she photographed are now gone. Fortunately, special rescue tools exist precisely for such cases. You get to work immediately, hoping to make your friend happy.
Warning
All of the tools discussed here can certainly save data, but if used improperly or carelessly, they can also cause permanent loss. The author and publisher assume no liability for corrupted data. If in doubt, please call in a professional data recovery lab. This is also the right choice if your hard disk is mechanically damaged or you can hear the read head hitting the disk.
Don't Panic
To avoid causing even more damage, it is important to keep calm in this kind of emergency. If you see a read error during normal operation, make a backup of the disk immediately, thus rescuing the remaining readable files at least (see the "Examination Board" box). As in the digital camera example here, if you are missing multiple files and directories or experience severe read errors, switch off the power quickly. This is the only way to prevent further writes, which would exacerbate the damage. The approach that follows will help you save not only hard disks, memory cards, and SSDs, but also scratched CDs, DVDs, and Blu-rays – assuming the disks do not use copy protection.
Examination Board
Modern hard drives and SSDs monitor their health state and will even tell you the results on request from smartctl. On Ubuntu, it resides in the smartmontools package [1]. Working as root, you can query the health status of the first hard disk using:
smartctl -H /dev/sda
If FAILED appears, the disk or SSD is already defective, or the risk of failure is great. In any case, you should stop operations and immediately make a backup. The badblocks tool can test any device for bad (data) blocks. To check, for example, the sde1 partition, you can run the
badblocks -sv /dev/sde1
command.
The test can take some time to complete; checking a USB hard disk will take several hours. If the two tools do not report any errors, the medium itself is at least still readable.
First, you should enable physical write protection for the defective medium as soon as possible. This means that the rescue attempt cannot destroy the operating system, and the rescue tools cannot destroy the data. The memory card from the digital camera, in the case initially described, turned out to be a slightly older 2GB SD card; write-protecting it was easily accomplished by moving the small write-protect tab on the right side.
USB sticks, hard drives, and SSDs usually do not have a write-protect switch. For critical data, you can buy a write-protection adapter, as used in computer forensics. A hard drive or SSD with less important data can be removed and plugged into an external USB enclosure, which at least prevents the Linux system used to rescue data from arbitrarily using the same disk. This method is quite common with swap partitions – or partitions that Linux incorrectly assumes to be swap.
Where's Waldo?
Now you can boot the PC on which you want to perform the rescue. If it does not have Linux installed, you can simply boot from any Live CD. When Linux is running, connect the defective medium. An SD card, for example, can be slotted into a USB card reader and plugged into the Linux PC. Do not mount the data storage medium, even if Linux suggests doing so.
Next, you need to find out which device file you can use to access the defective medium. The command to help you with this is
blkid -o list
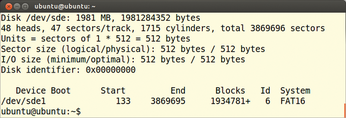
which you need to run as root, like all the other commands in this article. The command outputs a list of all the connected media and their device files (Figure 1). You can use the label column for orientation. The size of the partitions provides further evidence, as does the output by the
cat /proc/partitions
command (Figure 2).


Make a note of the name of the partition or entire disk that you want to rescue. In Figure 1, blkid identified a partition with the device name /dev/sde1 (Figure 3). If the programs cannot find any partitions, that doesn't necessarily mean all is lost: You can then call fdisk -l, which lists all connected data storage media. In this case, you need to make a note of the device file for the complete volume; in the example, this is /dev/sde.
Clone Wars
Trying to restore files directly on the failed disk is not a good idea. The risk that the tools destroy even more of the data is simply too great, and then you have no way to make a second rescue attempt. Therefore, it is advisable to first make a bit-perfect copy of the volume.
Of course, the hard disk on the rescue PC must have enough free disk space for the copy, and you need to store the restored data somewhere. Consequently, at least two, and preferably three, copies of the entire data storage medium should fit on the disk. For a 2GB memory card, you should therefore have at least 6GB of free space on the rescue disk. If you need to save an entire hard disk instead of just a partition, you might need to install an additional empty, larger hard drive to recover the data.
The duplicate itself is created with a small tool named GNU ddrescue [2], which reads a medium bit-by-bit and stores the content into a file known as an image. You will generally need to install ddrescue via the package manager; in Ubuntu, it is in the gddrescue package. GNU ddrescue has replaced the dd_rescue tool in many distributions; in some repositories, you will even find both tools.
The two programs differ in terms of their parameters and their approach: The newer ddrescue reads from the disk in quite large steps, skipping bad blocks first. After it has copied the good blocks, it checks the bad blocks again and tries to read as much data as possible from them.
The program remembers its actions, so you can interrupt the read operation and then continue some time later. This is particularly useful for large disks because reading can take several hours. In contrast, dd_rescue first attempts to identify the unreadable sectors. If you have a choice, you should go for GNU ddrescue.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.

