Building an IRC Bot with Cinch
Bot Tech

© Lead Image © Chris Modarelli, 123RF.com
Chat rooms aren't just for people. We'll show you how to access an IRC channel using an automated bot.
IRC, the Internet Relay Chat has existed for 20 years, and it is still a popular communication channel in open source projects and businesses. For almost as long, automated bots have listened on IRC channels and responded to user commands. The article shows how IRC bots can make themselves useful by helping you manage tickets and prepare documentation.
Spoiled for Choice
To develop an IRC bot today, you no longer need to learn Tcl to activate the bot ancestor Eggdrop [1]. Frameworks for bots are available in virtually any language (Table 1). Although I focus here on Cinch [2], a framework written in Ruby under the MIT license (Figure 1), you can easily adapt the code examples presented in this article to other languages.
Table 1
A Selection of IRC Bots
| Name of Bot | Programming Language | License | Website |
|---|---|---|---|
| Autumn |
Ruby |
Freeware |
|
| Willie |
Python |
EFL |
|
| PHP IRC Bot |
PHP |
CC-BY-3.0 |
|
| Jsircbot |
JavaScript |
GPLv2 |
|
| Java IRC Bot |
Java |
GPLv2 |

Cinch comes with an object-oriented API and a modular plugin system. Thanks to many unrelated plugins, a single bot can perform all kinds of tasks. To an IRC server, Cinch – as is typical of IRC bots – appears as a normal client. Therefore, it does not matter which system the bot runs on, whether on the same system as the IRC server or remotely on a developer machine. Nor does it matter which server software you use, as long as the server is a compliant implementation of IRC.
Bot on Board
Assuming you have a Ruby installation in place, you can install Cinch as follows:
gem install cinch
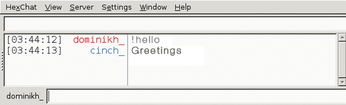
A simple bot named hellobot.rb (Figure 2) that responds to salutations in the form of !hello is presented in Listing 1.
Listing 1
hellobot.rb
Typing ruby hellobot.rb brings the bot to life; it then connects with the IRC server <IRC_server_address> and joins the channels <#a_channel> and <#another_channel>. If an IRC user types !hello in one of these channels, the bot responds with a rather indifferent Hi there.
The sample code consists of two parts: The main part is the Greeter class (lines 4-11). Each class represents a single plugin that responds to one or more commands from the user; a command must begin with an exclamation mark. To match the commands, bot developers rely on regular expressions. For example, /(\d+)/ is a single argument comprising one or multiple numbers.
The second part (lines 13-20) takes care of configuring the bot. The program receives a name and an address at which it can log in. Line 18 also explains what plugins the bot should use. The configuration of the file does not change in the remainder of the article, so I can now move on to the actual plugin classes. Developers can easily extend the array of plugins; for more information on the API, check out the documentation [3].
GitHub Connection
Developers spend a huge amount of time processing tickets; little wonder their conversations often revolve around this topic. This article will show you how to build a bot that will control the GitHub ticket system. A plugin will support opening, closing, and finding tickets. At the same time, I want the bot to respond to references of the type repository/gh-ticket_number in messages by displaying the title status of the ticket in the channel.
GitHub's API [4] is based on HTTP and JSON and allows both read and write access to large parts of GitHub – including tickets. You can experiment with access using curl at the command line; Listing 2, for example, requests ticket number 13069 from the Rails project.
Listing 2
Ticket Request with curl
This (abridged) example shows how GitHub structures the information the bot requires to display tickets. The developer can access both public information (such as tickets from open source projects) as well as private tickets [5]. In the second case, however, you do need to authenticate. The API allows authentication either via O-Auth or classic HTTP, which is usually sufficient for an IRC bot. For in-house installations of GitHub, access to the API looks like this: http://<IP_address>/api/v3/.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.

