Quick and Easy File Transfer with netrw
Shell Scripts
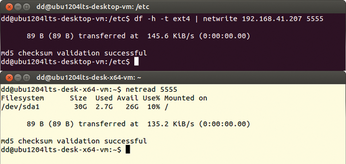
The two tools use the classical Linux approach – reading from standard input and writing to standard output – which makes it possible to send the output of a program directly to netwrite. You can omit the -o option or redirect the output of the data to appear on the screen of the receiving computer (Figure 5).
Mini Chat
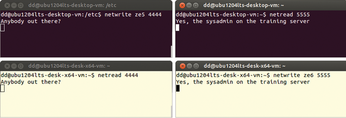
If you do not specify an input file or an output file, netwrite reads from the standard input and displays on the standard output. You can use this to build a makeshift chat tool (Figure 6).
If you intend to use this tool over a route outside of your private network, you'll want to secure the communication using Secure Shell (SSH). You need one terminal each for transmitting and receiving. Additionally, you must use a separate port for each direction.
Conclusions
The netrw tools make it easy to transfer data between two computers. They do not rely on any intermediate infrastructure and work practically on demand. And, if you encrypt the payload, you will always be on the safe side when transmitting data.
Infos
- Netrw: http://mamuti.net/netrw/index.en.html
- Code for this article: ftp://ftp.linux-magazin.com/pub/listings/magazine/163
- Stat (Coreutils): http://www.gnu.org/software/coreutils/
- Zenity: https://wiki.gnome.org/action/show/Projects/Zenity?action=show&redirect=Zenity
- Cdialog: http://freecode.com/projects/cdialog
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

