The sys admin's daily grind — Corkscrew
Dork Holiday

Sys admin columnist Charly never takes a vacation from the Internet. A beach bar with WiFi is quickly found, but it runs a forced proxy, which thinks that the SSH port (22) is in league with the devil and blocks the connection. Time to drill a tunnel.
The right tool for tunneling SSH through a proxy like Squid, Gauntlet, CacheFlow, Junkbuster, or Apache mod_proxy is Corkscrew. Why? Because the name corkscrew is well chosen, and because the program author introduces himself like this: "My name is Pat Padgett. I'm a dork." In my experience, such laconic people are great programmers.
Most distros have a Corkscrew in a back drawer somewhere; if not, you can pick it up online [1]. The SSH daemon should be running on port 443 on the target server, because many proxies refuse to connect to port 22. Incidentally, binding the SSH daemon to two or more ports simultaneously is not a problem. To do this, you just add another port line to your sshd_config:
[...] Port 22 Port 443
If you are already running HTTPS on port 443, you can set up SSLH [2] on your server as a last resort. This is an SSH/SSL multiplexer that makes it possible to operate SSH and HTTPS simultaneously on port 443.
If the proxy asks for login credentials, you need to store them in a file. Its name does not matter; I would use, say, /home/charly/.proxy-auth. Then, you can populate the file with data as follows: <Username>:<Password>
Getting Corked
Now you have to talk your SSH client into using Corkscrew. Edit the .ssh/config file in your home directory for this. (If it does not exist, simply create it.) You will be adding two lines:
Host * ProxyCommand corkscrew <myproxy.example.net> <3128>%h %p /home/<charly>/.proxy-auth
Of course, you need to change <myproxy.example.net> and the port number to suit your local situation. The variables %h and %p pass the parameters from the SSH call to Corkscrew. If you use a server without authentication, you just leave out the path to the username/password file.
Now, it's time for the premiere. The target server I use is a Raspberry Pi, whose sshd listens on port 443. The proxy is a standard Squid. As you can see from Figure 1, the login works fine – there is nothing to suggest that Corkscrew has a hand in the game, unless someone has access to the proxy logs. You would find the following entry, if you looked:
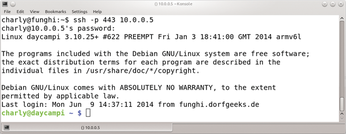
"CONNECT 10.0.0.5:443 HTTP/1.0" 200 <[...]>
But, who cares about logs while you're relaxing in a beach bar? Ah, they have WiFi.
Charly Kühnast
Charly Kühnast is a Unix operating system administrator at the Data Center in Moers, Germany. His tasks include firewall and DMZ security and availability. He divides his leisure time into hot, wet, and eastern sectors, where he enjoys cooking, freshwater aquariums, and learning Japanese, respectively.
Infos
- Corkscrew: http://www.agroman.net/corkscrew/
- "The sys admin's daily grind: sslh" by Charly Kühnast, Linux Magazine, Issue 111, 2010: http://www.linux-magazine.com/Issues/2010/111/Charly-s-Column/(language)/eng-US
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs

