Who pays free crypto developers?
Government Aid
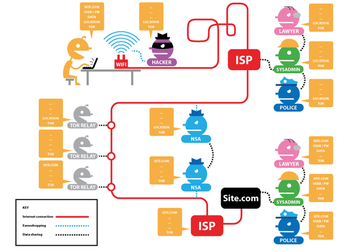
The Tor project, which enables anonymous surfing using encryption and numerous proxies, doesn't need the money of the CII, however. The project is financed mainly through larger donors; it gathered more than US$ 2 million in 2012, giving rise to suspicion: Although the project regularly publishes a report [11] listing sources of donations, they included various government organizations once again in 2012. Skeptics speculate that these offices are influencing the development work.
Even without the suspected backdoor, Tor is in the national interest of the US government, because it allows dissidents in authoritarian countries to communicate. The Tor project flatly denies the existence of a backdoor [12] and refers critics to the freely accessible source code for its software.
The Tor project's hosting costs are low because volunteers operate the network's computing nodes (relays; Figure 2); most of the money is spent on development, research, and marketing.
In Germany, projects actively need to seek support from authorities or governments and apply for appropriate tenders. In this way, the GnuPG project also received short-term financial support from Germany's BMI.
In some cases, companies also finance the complete development of a project. One prominent example of this is OpenVPN [13], which is backed by OpenVPN Technologies Inc. "Partners" generate revenue with support contracts and commercial VPN services. In such a model, however, the project depends on a single company, which alone decides which patches to accept and who reviews the software on its behalf.
Crowd Strong?
To raise more money, the GnuPG project started a crowd-funding campaign on Goteo in 2014 (Figure 3) [14]. This form of donation is only suitable for clearly defined objectives; the project wants to revise its website and fund new infrastructure with the funds raised. However, the developers first need to raise user awareness of the campaign and mobilize them. This requires massive work and advertising overhead. If the project hands out rewards depending on the amount of the donation, such as T-shirts, additional costs and other expenses arise.

Most projects are looking for one thing: more time for development. You can only get this if the dedicated developers have enough money to live on. As Werner Koch, the maintainer and creator of GnuPG, outlines in the interview, crowd funding does not typically provide permanent funding, and the figures for OpenSSL and GnuPG clearly show that donations alone cannot solve the problem in the long run.
Above all, projects in which the companies that benefit from the work employ the developers, or substantially finance the development work, seem to be successful.
As Marquess of the Open SSL project stated: "The ones who should be contributing real resources are the commercial companies and governments who use OpenSSL extensively and take it for granted.

Infos
- OpenSSL: http://www.openssl.org
- Heartbleed bug: http://en.wikipedia.org/wiki/Heartbleed
- GnuPG: https://www.gnupg.org
- Core Infrastructure Initiative on OpenSSL: http://www.linuxfoundation.org/news-media/announcements/2014/04/amazon-web-services-cisco-dell-facebook-fujitsu-google-ibm-intel
- Blog post on OpenSSL financing: http://veridicalsystems.com/blog/of-money-responsibility-and-pride/
- OpenSSH: http://www.openssh.com
- OpenSSH book: https://https.openbsd.org/cgi-bin/order?B09=1&B09%2b=Add
- PSW Group: https://www.psw-group.de/en
- OpenSSL consulting: http://opensslfoundation.com/what.html
- CII making progress: http://www.linuxfoundation.org/news-media/blogs/browse/2014/06/announcing-rapid-progress-core-infrastructure-initiative
- Tor financing: https://www.torproject.org/about/financials.html.en
- Tor Project on backdoors: https://www.torproject.org/docs/faq.html.en#Backdoor
- OpenVPN: http://openvpn.net
- Crowd funding for GnuPG: http://goteo.org/project/gnupg-new-website-and-infrastructure
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs

