Network Discovery
Using Zenmap
Download and install Zenmap for your platform. I use Zenmap on Linux, macOS, and Windows and have found that they all look and work the same, so there is no particular platform advantage. As the Zenmap documentation states, when installing on Windows, you might want to download and install the latest version of Npcap, rather than to rely on the one bundled with Zenmap.
Launch Zenmap and look at the interface (Figure 1).
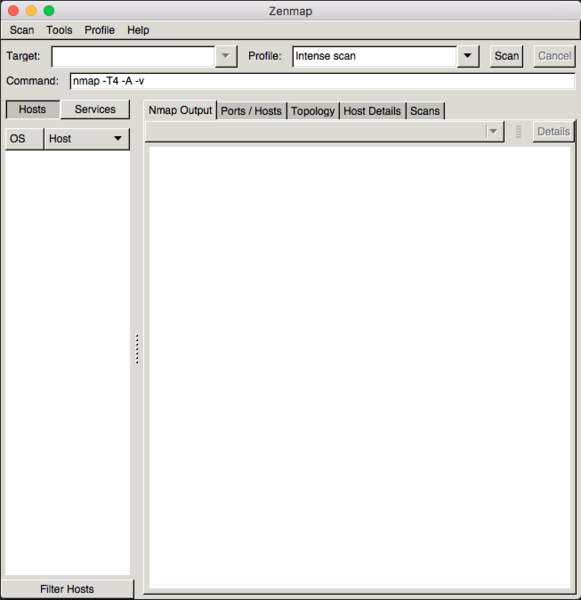
Zenmap’s default scan setting is Intense Scan, and the command-line equivalent of that command is shown in the Command field. You only have to supply a target for the scan. The target can be a single host, a network, or a web address. For an initial test, select an IP address or a hostname on your network, enter it into the Target field, and click Scan. It will take a few minutes for the scan to complete.
While that Intense scan runs, let’s take a closer look at it. In the Command field, you see nmap –T4 –A –v <hostname or IPaddress>.
The –T4 parameter is a timing template, and 4 is the level (aggressive). The levels range from 0 to 5 (see Table 1).
| Table 1: Timing Template Levels |
|
| 0 |
Paranoid |
| 1 |
Sneaky |
| 2 |
Polite |
| 3 |
Normal |
| 4 |
Aggressive |
| 5 |
Insane |
Timing values in the 0-2 range are less likely to set off network IDS alarms; they also take a long time to run, especially if the network is large. Even segmented /22 networks can take hours to scan and that’s not realistic for everyday security scanning. The documentation recommends level 4, which is right for most authorized network scans on today’s faster (1GbE) networks.
The –A option is an aggressive scan that includes other options such as OS detection, version scanning, script scanning, and traceroute. There is no need to add these options if you use –A. This option is not recommended when you want to scan a network with a bit of stealth. And the standard is -v (verbose mode), which you definitely want regardless of your scan purpose to acquire the most information possible about your target or targets.
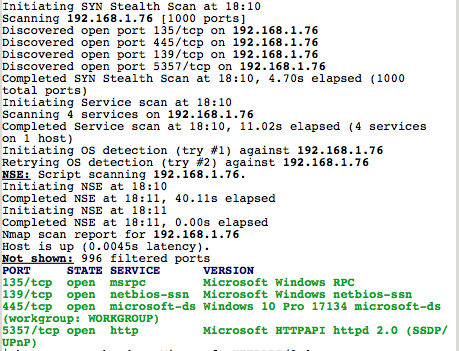
Figure 2 shows the results of my scan of a Windows 10 system.

However, Figure 3 specifically calls out the most important data for this scan: open ports and their versions. Focus on the 445/tcp line that gives you the information you need for security purposes: Windows 10 Pro 17134. This information is significant, because it tells you, with a little googling, that this system is out of date and could have multiple common vulnerabilities. For the hacker, this information is gold, because it tells them that the system administrator or system owner is not particularly diligent with updates.
Taking a wider tour of Zenmap, you’ll see multiple tabs (Figure 4): Nmap Output, Ports/Hosts, Topology, Host Details, and Scans. Of those, Ports/Hosts and Host Details are the most interesting.
The Ports/Hosts tab reveals a more human-readable format than you saw on the Nmap Output tab in Figures 2 and 3.
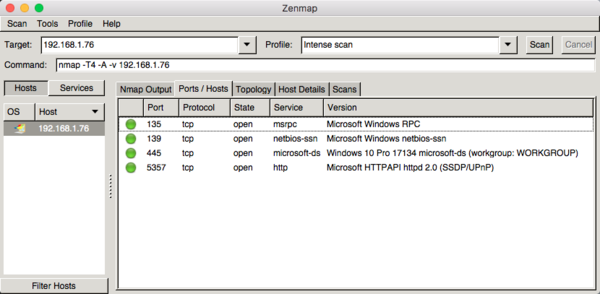
The Host Details tab (Figure 5) reveals more information, although it is not necessarily 100 percent accurate. For example, the scanned system is a Windows 7 Pro computer upgraded to Windows 10 Pro, but identified as Server 2008 SP1 or Server 2008 R2, with an 86 percent confidence level of accuracy.
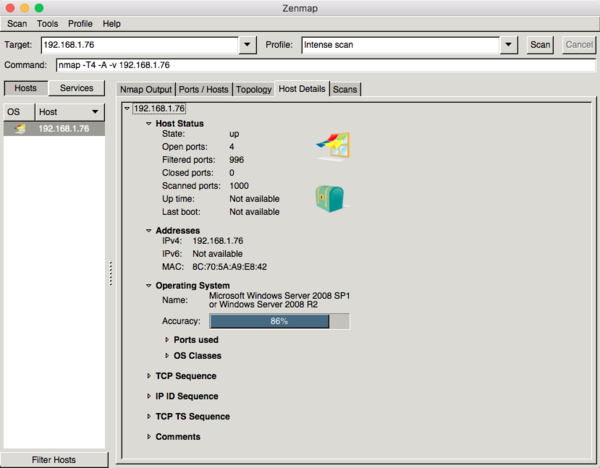
Although Nmap misidentifies the system on this tab, the Ports/Hosts tab gave an accurate assessment of TCP port 445: Windows 10 Pro 17134.
Scanning Profiles
Zenmap allows you to save your scans so that you can refer to them later, and you can compare scans from two different times. Profiles are one of Zenmap's most compelling features. From the top menu, click Profile, and select New Profile or Command.
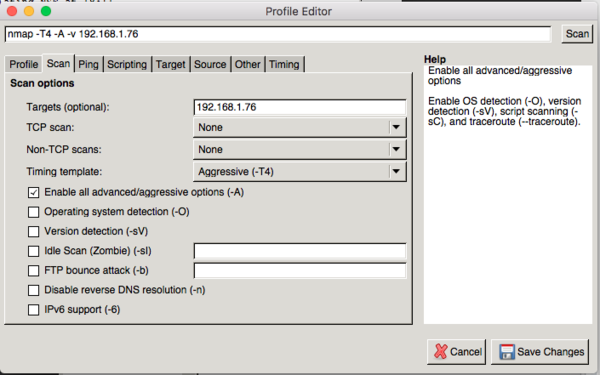
You’re presented with a new Profile Editor screen (Figure 6) that allows you to select from dozens of options. From the Scan tab, you can select TCP scan, Non-TCP scans, and Timing template, in addition to other options under the Ping, Scripting, Target, Source, Other, and Timing tabs..
Once you’ve saved the Profile, you can use it to scan at any future time by selecting it from the Profile drop-down list. You can selectively edit the Profile or save the changes as a new Profile. The Profile Editor requires that you name a new Profile or you have to Cancel and lose your changes.
Summary
Zenmap and Nmap are cross-platform tools that are essential for security professionals, as well as any system administrator with security responsibilities. This article provides a very brief scratch-the-surface overview of Zenmap. Zenmap is a professional security tool that provides you with a great deal of information about your network and its components. You can detect open ports, operating systems, and service versions with it. It is a powerful tool for hackers as well, which is why its use is often scrutinized and frowned upon in some settings.
No tool is perfect, but Nmap and Zenmap come pretty close to the perfect network discovery tools. They’re free and open source, which pushes them even closer to perfection. But remember that a tool and a weapon are often only separated by the intent with which they are used. With great power comes great responsibility.
« Previous 1 2
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.

