Tethering
Using the mobile Internet
ByThanks to the modems built into today’s smartphones and tablets, you can use fast mobile Internet from almost anywhere. The mobile devices can also get your laptop online.

Only a few years ago, if you wanted to access the Internet from on the road, you needed a laptop with a UMTS stick – a USB-based wireless modem that acted as an interface to the cellular network through the Universal Mobile Telecommunications System (UMTS) standard. Modern smartphones and tablets are quickly changing all this. Mobile devices are now a practical choice for accessing services such as email, Twitter, and Facebook from anywhere in the world. However, the limited displays on these devices do not let you do everything conveniently, which can mean turning back to your laptop.
A huge number of USB modems are available. Most cell phone service providers have something in their portfolio, although there are just a handful of USB modem manufacturers. The support for these devices on Linux has improved dramatically, but Linux users can still face setup orgies with some models. And it isn’t much consolation that Mac OS X users also complain of poor drivers and scary dial-up software.
If you experience issues trying to set up a USB modem, or if they are simply too clumsy for your liking, check out the alternatives currently available on the market. The most convenient choice is a laptop with a built-in USB modem: Simply plug your SIM card into your laptop, and you’re done. This removes the need for annoying peripherals and guarantees well-integrated drivers – although they still might not be perfect under Linux. Because there aren’t too many vendors who have taken this path thus far, the offerings are few and far between. In fact, the technology is normally only integrated into more expensive business laptops.
MiFis are an interesting alternative to USB modems (Figure 1).

These are mobile hotspots that use a plugged-in SIM card to open a connection to the cell network and then pass the data on to your computer via USB or WLAN. The latter variant removes the need to install problematic drivers or proprietary dial-in software, as the MiFis act like normal WLAN hotspots from the computer’s point of view. You just enter your access credentials and the connection comes up. The devices, which are about as big as a matchbox, offer one other benefit: They provide access for up to five devices at the same time, which is perfect for tradeshows, for example.
Best of All Worlds
If, however, you want to avoid additional gadgets, you can simply use your smartphone. Most users carry theirs with them all the time anyway, and today’s plans often include a flat rate for Internet access. And, state-of-the-art phones often achieve data throughputs not far behind DSL thanks to Evolved High Speed Packet Access (HSPA+), which is a UMTS extension that supports higher data rates. So, why not use your phone to take your laptop onto the Internet? The magic word here is tethering, and it combines the best of both worlds.
Tethering causes the phone to open an Internet connection and pass the data to other devices via USB or WLAN; in effect, it becomes a mobile hotspot. As with MiFi, you don’t need to install any drivers on your laptop. Instead, you access the smartphone or tablet via WLAN, just like at home or in a hotel. Tethering also solves another problem: Depending on your provider, you will only be given one SIM card per plan. This means continuously unplugging and plugging it back into your USB modem and phone. With tethering, the card stays in the phone, so you don’t need an additional data plan.
Tethering with Android
The latest generation of Android devices supports tethering out the box. Our lab devices are a Samsung Galaxy S2 with Android 2.3.4 and a Samsung Galaxy S GT-I9000 with Android 2.3.3. Because phone manufacturers and cell network providers tend to grow their own flavors of Android, the numbers may differ if they use the same version of Android. In this case, look for settings such as Mobile Access Point or Mobile WLAN Hotspot.
Before you set up the hotspot, make sure that you have configured your smartphone correctly so that it establishes a mobile Internet connection with your USB modem provider. Our test device set up the required APN (Internet access point of the cell network operator) without any intervention. Many providers also offer to text you the correct settings, but this can be a trap because some providers assume a special APN for certain rates and then bill you for horrendous amounts if you use a different access point. When in doubt, ask your provider for the correct configuration.
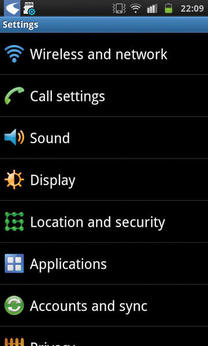
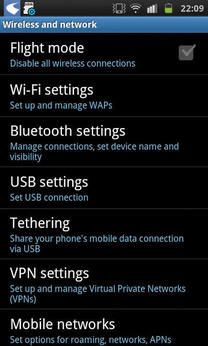
Once your smartphone is on the Internet, you can set up tethering. To do so, open the Settings (Figure 2) and then select the Wireless and networks function to display a dialog similar to Figure 3.
In Tethering and portable hotspot for the Galaxy S2 (Figure 4) and Tethering (for the Galaxy S), you will find the sub-items Mobile AP (Galaxy S2) and Mobile AP settings (Figure 4). These are the focal points for options relating to the mobile hotspot (Figure 5).
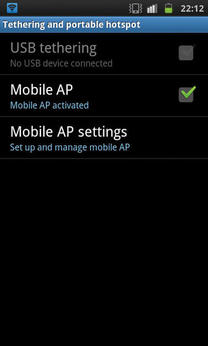

The configuration is quite simple in both cases. The SSID is preset to a value that you can edit as needed. The test devices don’t hide the hotspots, but this is only security by obfuscation. Choosing a secure password and a good encryption algorithm is more important. To prevent attackers from guessing it, your password should be at least eight digits, preferably ten, and include upper- and lowercase letters, numbers, and non-standard characters.
Encryption is also important. In our lab, the Galaxy S2 gave us a choice of WPA2 PSK and Open. The latter opens up the hotspot to the general public and is an option you will want to avoid. An open hotspot not only means that anybody can use your connection to access the Internet, it also means that you are responsible for the consequences. Some providers give you unprotected access to the online customer interface if you dial in using your SIM card. In the worst case, a third party might change your data and order things in your name.
Once you have chosen a secure password for encryption (WPA2 PSK), click on Save and check the Mobile WLAN Hotspot box. The operating system tells you that this will increase the power consumption. Click OK and the status bar will tell you that the hotspot is active. You can continue working in the normal way with your phone; the hotspot service runs in the background. A blue icon shows you that it is active.

To quit tethering, go back to the menu and disable the Mobile access point (GT-I9000) or Mobile WLAN Hotspot option (Galaxy 2).
Tethering with Other Devices
Devices with other operating systems support tethering, too. The problem is that the provider often can choose whether they enable this feature. Some cell providers block tethering and offer their users an expensive add-on plan, and early Android devices also didn’t offer tethering out the box. Some rumors claim that the function is blocked on certain devices in the current version. Although you always have the option of installing the hotspot feature in the form of an add-on program, this often means jail breaking or rooting the device, which will probably void your warranty.
Watch Out
Although tethering is easy and convenient as a general rule, a number of pitfalls must be considered. Because the system is permanently transferring data, limiting smartphone tethering to cases where you have Internet access (WLAN or UMTS) is a good idea. Surfing the mobile web at HSPA+ speed and without a plan to cover it will break your budget within a couple of minutes. Be sure that you have an unlimited data plan; otherwise, there is nothing you can really do to monitor the amount of data you are transferring. Although tools such as the Android RadioOpt Traffic Monitor app can help you keep track, they will not automatically interrupt the connection once you use up your data allowance. If you use your phone somewhere outside of your home country, the prices for mobile data transfer can be horrendous.
Be sure to read the small print in your data plan. Many providers slow down the speed once you exceed a certain data volume, and others charge you extra. Flat-rate plans are not always well-suited for going online with a laptop. Many providers offer cheap plans, but you can only use them with your phone, as well as more expensive plans, which include laptops. After you have checked your options and are sure you can avoid the cost trap, there is nothing to stop you from enjoying a spot of mobile surfing.
Conclusions
Being online on the road isn’t a luxury today – it’s affordable and easy to achieve from a technology point of view. If you prefer to avoid using a USB modem, a tethering solution or a mobile hotspot are options. Thanks to WLAN, both approaches will work with almost any device and can be set up with just a couple of clicks.
Although tethering is available on virtually any modern cell phone, mobile hotspots impress with good battery lifetimes. In our test, we achieved better online speeds – compared to MiFi access – with tethering, which is something you’ll notice if you need to transfer larger volumes of data.
The Author
Florian Effenberger has been a free and open source evangelist for many years. Pro bono, he is Chairman of the Board at The Document Foundation. He has previously been active in the OpenOffice.org project for seven years, most recently as Marketing Project Lead. Florian has ten years' of experience in designing enterprise and educational computer networks, including software deployment based on free software. He is also a frequent contributor to a variety of professional magazines worldwide on topics such as free software, open standards, and legal matters.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
