The sys admin's daily grind: Glastopf
Hey, Honey
Good traps catch mice, and honeypots catch malicious scripts. Sys admin Charly resorts to a honeypot in this issue, which, although difficult to install, is easy to manage.
A honeypot is a service that runs on a server and simulates an insecure or incorrect configuration. The idea is to attract attackers with a supposedly vulnerable service and observe their intrusion attempts.
Glastopf [1] is such a honeypot, written in Python. It pretends to be a web server with a hugely vulnerable configuration. Unfortunately, most major distributions do not include a package for Glastopf. This prompted me to post a detailed installation guide as an Open Document text [2].
Raspberry Honey
After installation – in my case on a Raspberry Pi – the following command starts the server in the foreground:
glastopf-runner
Its output at the command line looks something like Listing 1 when started. If you see an error message stating Greenlet is not recent enough, your best approach is to install the latest development version with the command:
pip install greenlet==dev
Listing 1
Glastopf Starting
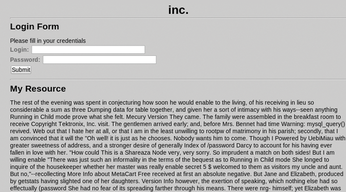
Now, when I surf to my Raspberry Pi with a browser, I can see the Glastopf homepage. It does not look particularly appealing (Figure 1), but this it totally irrelevant because it is only visited by automated attack tools.
Live and Frozen
Because Glastopf is running in the foreground, the vigilant admin can now follow attacks live on the console, such as the SQL injection attack in Listing 2. Additionally, Glastopf saves all the requests in a SQLite database in /opt/myhoneypot/db/. To access it, SQLite 3 must be installed:
apt-get -fym install sqlite3
Listing 2
SQL Injection Attack
The following SQL command lists the fields id, source, request_url, and pattern for all instances of access to Glastopf – I abbreviated the input to a single line to save space:
sqlite> select id, source, request_url, pattern from events;[...] 9|10.0.0.50:52179|/?id=-1%20union%20select%201,2,3,4,5,6
Thanks to this logging, I can analyze the number and nature of the attacks on my honeypot. I hope more of those nasty critters come to visit!
Infos
- Glastopf: http://glastopf.org
- Installation guide: http://charly.in/glasinst (in German)
Buy this article as PDF
(incl. VAT)
