Graphical tools for firewall configuration
fwbuilder
Firewall Builder (fwbuilder) [5] is a dinosaur among the firewall graphical configuration tools with more than 10 years of continuous development history. Accordingly, the software is well positioned on the market and can be found in the repositories of almost all major Linux distributions. Fwbuilder manages firewall systems across platforms and is therefore also suitable for use in heterogeneous environments with Cisco firewalls and BSD's Packet Filter (PF) [17], in addition to iptables.
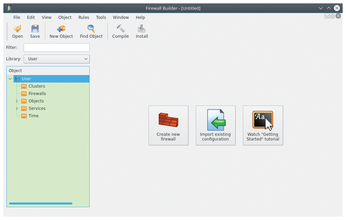
On Linux, fwbuilder configures iptables with automatic rule validation; it even supports IPv6. The installation adds fwbuilder to the menu structure of the respective desktop. On first launch, you will see two windows: In addition to the configuration window, the routine also calls a smaller Quick Start Guide that introduces the most important functions of the program to new firewall administrators.
In the straightforward configuration window (Figure 6) is a menu at the top with a buttonbar below for quick launching of the most important functions. On the left is a tree view with various objects. On the right, two buttons let you create a new ruleset or import an existing ruleset. A third button calls the system's web browser and opens the Quick Start Guide [18] on the project page.
Wizard
Clicking the Create new firewall button opens a dialog that helps you to define new rules with a wizard. The wizard already has templates with useful settings for default firewalls; additional protection rules can be implemented easily.
The objects on the left in the program window contain rulesets and can be organized and extended as object libraries. Interfaces or services also appear as objects. First, you specify a new object name and then tell the routine which firewall – typically iptables for current Linux distributions – and which operating system to expect host-side. Because the firewall selection list correlates with that of the operating systems, the software usually automatically enters the appropriate operating system correctly when you choose a firewall. In the dialog box, you then specify whether you want to use preconfigured rulesets.
Clicking on Next takes you to the next dialog. If you want to create the objects manually, the dialog reveals which physical interfaces the system includes. You can search for interfaces via SNMP if it is installed on the host. In the following dialog, define the individual interfaces including the respective mode for IP address assignment. After a final click on Finish, the software creates the new object library (Figure 7).
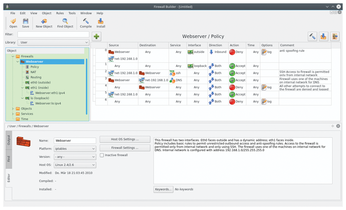
The program window now splits into three areas, with the right pane broken down into a pane for rulesets and another for processing steps, in which you can change individual settings (e.g., for the interfaces). The ruleset is based on iptable syntax; you can extend it by clicking on the green plus symbol in the top left corner of the list. As is usual with iptables, new rules require that all packets are rejected first.
You can drag individual objects from the segment with the object libraries and drop them at the desired position in the ruleset. Fwbuilder then automatically adapts the rule to your specifications. If objects are still missing in the library (e.g., if a user adds additional hardware to a host computer), admins can add them at a later time.
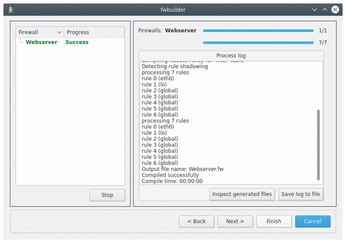
Once all rulesets are in place, you need to compile the rules to match the syntax of the respective firewall. The supported host systems range from Linux through various BSD derivatives to Cisco and HP appliances and have very different syntaxes. To proceed, click on the hammer icon in the upper-right corner of the rule list. In the last step, the compiled firewall is transferred to the host system using SSH and SCP (Figure 8). However, if fwbuilder is already running on the host system on which it acts as the firewall, you can click on the Compile and install this firewall button.
You can subsequently compare modified or supplemented rules with the original rulesets to filter out inconsistencies. To do this, select Tools | Find Conflicting Objects in Two Files and specify the files with the rulesets. The software then automatically checks these for inconsistent entries. This is especially useful wherever very complex rule sets and mutual dependencies can cause the admin inadvertently to misconfigure objects when changing the rules.
Gufw
The relatively new Gufw project [6] sees itself as a graphical front end for the Uncomplicated Firewall (UFW) [19], which acts as the default defense for Ubuntu and its derivatives. Gufw and UFW are now available for most of the major Linux distributions and are also included in their software repositories. Like fwbuilder, the dynamic duo UFW and Gufw require netfilter and iptables on the system and can handle both IPv4 and IPv6. Unlike fwbuilder, Gufw does not work across platforms. However, the GUI can be used to manage UFWs on remote computers.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.

