Virtualizing complex Linux systems
It's Complicated

© Lead Image © Shawn Hempel, 123RF.com
If you are ready to migrate your hardware RAID system to the virtual world, standard virtualization and forensics tools are ready for the task.
Ever since the virtualization epidemic hit the datacenter, server filesystems have increasingly taken the form of images, and conventional partitions have been on the decline. The benefit for the admin is that the filesystem images are easier to move or manipulate.However, if you want to use physical disks – typically block devices named /dev/sd<x> or the like – in your own cloud, you need to convert them to suitable virtual disk image formats, such as .vdi or .vmdk.
Popular conversion programs, such as qemu-img --convert (for KVM), can convert your physical partition to a virtual form, but these tools are not designed to address complex situations. For instance, if you want to build a RAID system from multiple disks, you need to master a few tricks, and this article will help you do so. Incidentally, the approach described here relies on forensic tools, because I developed this technique while investigating a crime case. For virtualization, I will rely on VirtualBox [1] version 4.
Problems with RAID Controllers
Physical systems are not always easy to virtualize. For example, you can experience driver problems if the hard disks come from machines in which the RAID systems are managed by hardware controllers. Some tools do exist for simple scenarios. KVM offers a number of options for smoothing out the process. If you rely on VirtualBox, you can easily convert a hard disk /dev/sdb by using:
VBoxManage convertdd /dev/sdb test.vdi --format VDI
This command converts the currently mounted disk, which you might have removed from another host, to a virtual hard disk named test.vdi using VirtualBox's own Virtual Disk Image (VDI) format [2].
Images like this can almost always be integrated easily into any new guest system, but other hypervisors can also handle them. Once this (fairly time-consuming) process is complete, you can export the entire system as an appliance in Open Virtualization Archive (OVA) format [3].
Complex Servers
Unfortunately, a typical server system rarely uses just a single hard disk. You are more likely to find a setup in which one hard disk stores the system, and the data resides on a RAID array. If the original host consists of three hard disks (e.g., a 40GB SATA and two 80GB SATA disks on a RAID controller), you can expect the conversion to be more complex.
If you can bring the legacy host back to life, you have many options. But if you don't have access to the original system (e.g., when the hard disks were part of the evidence in a crime case), the following approach can help. To read alien hard disks, administrators often resort to the RAW format, because it is the simplest possible standard and practically any version of Linux has suitable tools for it.
However, forensics experts tend to prefer the Expert Witness Format (EWF), which was introduced in an article in a previous issue of Linux Pro Magazine [4]. EWF offers a variety of benefits that help admins manage complex tasks. The ewfacquire program creates images in EWF; you need to install the ewf-tools package from your distribution's repository to access the tool.
Striped Set: RAID 0 – A Tough Nut
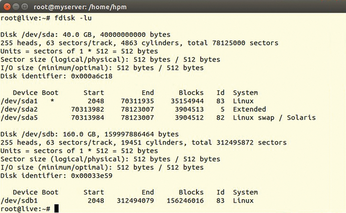
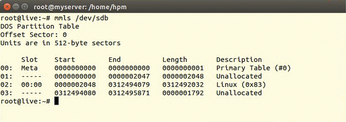
The use of a striped set (RAID 0) is not recommended from an administrative point of view, but you still see it on older servers. Because it causes the biggest problems and was used on the original system, I will be using it as an example here. Given a working controller, fdisk will show the disks that belonged to the striped RAID set (Figure 1). The forensic counterpart to fdisk from The Sleuth Kit is mmls (Figure 2).
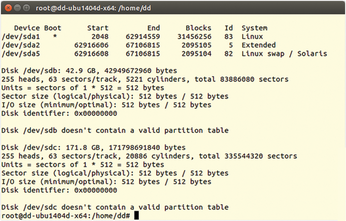
If you take the hard disks out of the legacy system and mount them on another machine without a RAID controller, things change. Although nothing changes for the first hard disk, you will see, as in Figure 3, that disks 2 and 3 (the two 80GB storage media) are no longer a system; in fact, they do not even contain a partition table, according to fdisk.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs

