Securing the Linux kernel with lockdown mode
Using Lockdown Mode
To use lockdown mode, you need to call the lsm and lockdown parameters in the Linux kernel command line. The kernel command line (the command that actually starts the Linux kernel) is executed during the boot process – see your Linux distribution's documentation for more on adding Linux boot parameters. The lsm parameter activates the LSM subsystem and expects the lsm=lockdown,yama arguments for lockdown. If LSM is already activated for other modules, you just need to append lockdown and yama, separated by a comma, to the existing parameters. The lockdown parameter can have two arguments: integrity and confidentiality. I'll tell you more about lockdown's integrity and confidentiality modes later in this article.
In principle, lockdown mode can still be activated at run time by calling echo confidentiality or echo integrity with a redirect to the /sys/kernel/security/lockdown file. Of course, lockdown mode cannot be disabled at run time in either of these two scenarios. Enabling at run time is not quite as secure as enabling from the command line, because full protection does not kick in right from the first second (Figure 2).

Integrity and Confidentiality
The developers offer two modes of the lockdown implementation. Integrity mode ensures that root cannot modify the currently running kernel. It implements what the developers originally wanted to achieve with the entire lockdown patch: that ability to establish the chain of trust between the running kernel and the originally started kernel.
In the meantime, however, lockdown mode has evolved. In addition to protecting the running system, the developers also focused on protecting any content that may currently be present in RAM. Root can access RAM and read it at will. This is precisely what confidentiality mode prevents. If confidentiality mode is active, the attempt to read memory will fail. Keeping users from reading memory significantly reduces the risk of passwords or other confidential data falling into the hands of attackers.
If you take a look at the Linux source code (Figure 3), you will see the concrete functions that the two lockdown modes trigger in the background. If the kernel is running in integrity mode, loading unsigned modules is prohibited. You can also no longer use kexec to make the system boot directly into a new kernel.
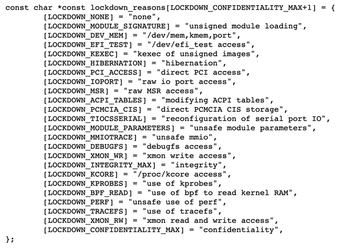
Several modules in the Linux kernel offer functions that are explicitly marked as "insecure." In integrity mode, the kernel prevents root from using parameters that load such modules. If a user of the root account tries to use a parameter that loads an insecure module, the user will immediately see a Permission Denied response from the kernel. MMIO operations that are identified as insecure are also prevented by the kernel, as are certain ways of using perf. Another important fact: It is basically possible to modify the running kernel using a system's ACPI tables and thus compromise the kernel. This explains why integrity mode also deactivates these operations across the board. Also interesting for mobile systems: Lockdown mode deactivates the hibernation feature.
Confidentiality mode adds several additional constraints. Access to /dev/mem, /dev/kmem, and /dev/port is prevented by the kernel. Traffic on serial ports cannot be read by root. Access to debugfs for debugging purposes is disabled, as is access to /proc/kcore. Even with the Berkeley Packet Filter (BPF), you can no longer read kernel RAM directly.
Compatibility Problems
Lockdown mode disables various features that are used by userspace software. Many of the functions that lockdown mode disables are explicitly intended for debugging only but have existed for years or even decades. The fact that various userspace software tools have come to rely on these functions means that some applications might not work after you enable lockdown mode.
The kernel developers therefore view lockdown as an optional feature that is not enabled by default. If you want to use lockdown, plan some time and investigate whether your software works in the usual way after locking down. This is especially true for confidentiality mode. If confidentiality mode isn't right for your systems, you might still be able to use integrity mode, which prevents attackers from systematically opening up security holes.
« Previous 1 2 3 4 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs
-
Juno Computers Launches Another Linux Laptop
If you're looking for a powerhouse laptop that runs Ubuntu, the Juno Computers Neptune 17 v6 should be on your radar.

