Implementing Zero Trust Security
Aiming for Zero

Some old-school admins are still philosophizing about secure internal networks, but the experts have already moved on: Zero trust architectures use a reliable but complex strategy to protect the network from all threats – inside and outside.
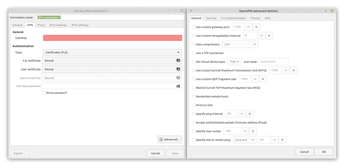
In the third year of the coronavirus pandemic, it has now long been clear that many companies are likely to remember the virus as beneficial to their own business. VPN solution vendors definitely fall into this category: When home office and teleworking mutated from the exception to the rule in many companies, existing VPN solutions became substantially more in-demand. Hardly anyone expected the load on the VPN gateways to explode overnight. The large network manufacturers were happy to help out their customers as many admins purchased more powerful systems for OpenVPN (Figure 1).
But do VPNs really solve the problem of network security? Many experts are not so sure. Implicitly, all parties involved with VPNs start from the following premise: There is a difference between the internal and the external network, and it is safe to treat internal clients differently from external clients. VPNs are regularly used specifically because admins do not want certain services to be accessible from the Internet at all. In many companies, VPNs form part of a security architecture that has grown organically over many years. Because security requirements have increased continuously over the past two decades, companies have invested more and more money in private networks and cut off more and more services from the outside world.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Ubuntu Core 26 Offers Game-Changing Enterprise Features
Ubuntu Core 26 could be a game-changer for organizations looking for increased security and reliability.
-
AI Flooding the Linux Kernel Security Mailing List
AI is giving Linus Torvalds a headache, but not in the way you might think.
-
Top Priorities for Open Source Pros Seeking a New Job
Professional fulfillment tops the list, according to LPI report.
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
