Facebook releases its own OOM implementation
Always on Your Guard
OOMd is also modular. In addition to PSI, the service relies on cgroups v2 under-the-hood; this is a kernel-based function for limiting and assigning resources and permissions. OOMd does not force the implementation of cgroups but uses cgroups v2 only as a second data source for its own monitoring of the system with a focus on RAM.
The dominant principle behind OOMd is that caution is far better than indulgence. Monitoring plays an important role: Unlike the kernel implementation of the memory killer, OOMd is designed to take action before a system-wide OOM situation occurs. To this end, the service continuously scans its main data sources – cgroups and PSI – and, in the event of an issue, automatically takes action before a genuine OOM situation actually occurs (i.e., before a malloc() call fails).
Because OOMd resides in user space and not in the kernel space, it benefits from far greater flexibility, especially with regard to extensions. It is thus not surprising that Facebook has designed the OOMd with a plugin interface that can be used to load external functionality. The plugins are directly integrated into the OOMd workflows – but the only plugin that comes with the OOMd is the one for killing processes. However, many options are conceivable, such as the option of performing various other tasks on a system before killing a process.
Simple Configuration
OOMd is written in C++ and uses the JSON notation as its configuration format. The results are very clear: The cgroups directive allows different procedures to be defined for individual cgroups, where target stands for the target group to which the entry refers. The other entries in each cgroup directive determine, among other things, which handlers and actions are used for OOM events. Figure 5 provides an example that makes it quite clear how flexible OOMd is in practice.
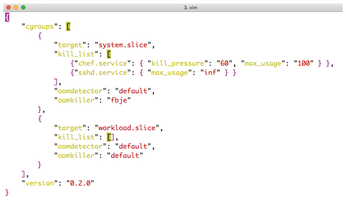
The example specifies that, when an OOM situation occurs, the chef service should be stopped first if it accounts for more than 60 percent of the total RAM load or has allocated more than 100MB of RAM for itself. The developers, however, have given the OpenSSH daemon (sshd) a survival guarantee; the max_usage:inf entry specifies that OOMd must never shut down the service under any circumstances.
This is also very useful, because without sshd, only a VNC or KVM console would remain for the remote login, and in the case of the kernel OOM, it is quite conceivable that the sshd would get into the firing line as one of many memory users. If you use OOMd, on the other hand, you can completely rule this out.
The Facebook developers heap praises on their own solution, by the way. In the documentation on GitLab, they state that the new OOMd has completely eliminated the previously described livelock situation that resulted in waits of 30 minutes or more.
Conclusions
Facebook brings an urgently needed and pleasantly fresh breeze into the OOM debate with its in-house solution: It now becomes clear that OOM is not a task that the kernel must handle. And it is also clear that functionality and flexibility can be achieved in user space that would be unthinkable in kernel space. The userspace OOM killer published by Facebook is interesting in this respect and will hopefully see rapid development.
And that additional development necessary: Currently, OOMd's functionality is limited to little more than what the existing OOM killer in the kernel can do. Nevertheless, Facebook explains that the tool works far better in everyday life than the original Linux solution. It is therefore almost impossible to predict what will happen if OOMd attracts a larger fan base and is available in packaged form for the usual distributions. It's quite possible that Facebook has succeeded in a real coup. One thing is certain: If you are looking for a virtual contract killer, you now have a choice.
Infos
« Previous 1 2 3 4
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.
-
New Pentesting Distribution to Compete with Kali Linux
SnoopGod is now available for your testing needs

