Using the Raspberry Pi as a gateway proxy
Gateway to the World

Extend protection to all of your Internet traffic with a Raspberry Pi minicomputer set up as a cost-effective external proxy server.
The Tor Project offers an option for obfuscating your IP address and thus hiding the most important clue to your identity on the web. When it is installed locally, you need to connect every single client application separately with Tor, which can be complicated. Moreover, the application must be able to communicate via SOCKS. If, instead, you choose to route your entire Internet traffic through the Tor network, your only option is an external router.
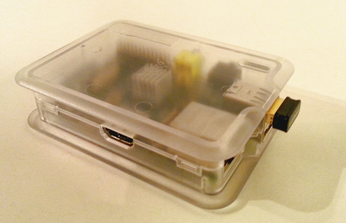
The Raspberry Pi (Figure 1) is ideal in this role because the hardware is cheap, and its power consumption is low. This project gained popularity as Onion Pi [1]. But, even as a Tor user, you should not rely on this solution alone for security. After all, obfuscating your IP address is only half the battle and cannot hide your identity on its own (see the "Tor Limits" box).
[...]
Buy this article as PDF
(incl. VAT)