WildFire and FlowScape are powerful new tools for intrusion detection
Open Source Instead
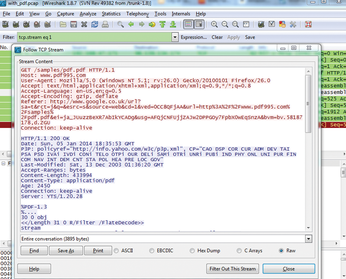
Open source tools also have advanced capabilities for dealing with APT attacks. For example, say you want to find PDF files from a large packet capture (pcap) dump. To do so, fire up Wireshark and click File | Export Objects | HTTP and go to the file containing a PDF. You can also pick up the PDF by looking in the filter file frame that contains %PDF (Figure 7).
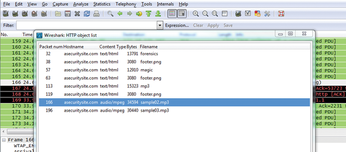
To find a music thief, such as someone who has downloaded a music file that you happened to catch in your pcap file, you again open Wireshark and click File | Export Objects | HTTP. Figure 8 shows a window listing eight files; if you click on the file that contains sample02.mp3, you can save it and deal with it later.
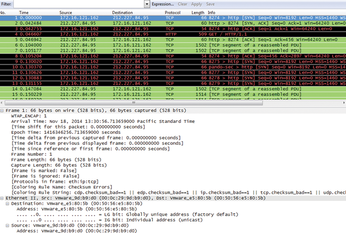
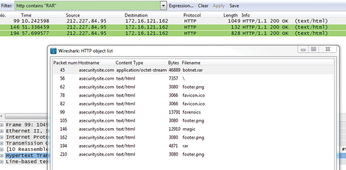
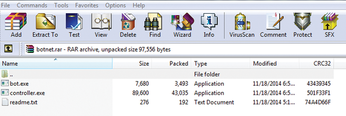
On the other hand, if you are looking for a RAR file that has been downloaded and is in your pcap file, how are you going to find it in a sea of files? As for the music file, open Wireshark (Figure 9) and click File | Export Objects | HTTP (Figure 10). The RAR file is the first file, botnet.rar, in the list. Click on the file and save it to your local machine. As you can see in Figure 11, the file contains a .exe along with a readme.txt.
Conclusion
In this article, I looked at some of the tools I work with on a daily basis. Palo Alto Networks' WildFire and CyberFlow Analytics' FlowScape are two examples of tools in my arsenal that I use to keep the badness at bay. The last tool, Wireshark, is one of the best open source packet analyzers available today.
« Previous 1 2
Buy this article as PDF
(incl. VAT)
