Nine steps for securing an Android tablet
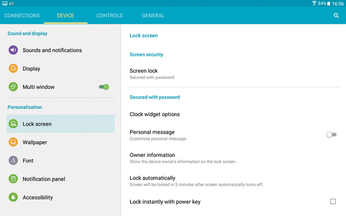
Set the Screen Lock
Because a tablet is portable, privacy is more of an issue than on a workstation. Tablets may offer several levels of security; from least to most secure, they are: the selection of parts of a pattern in a certain order, a PIN, or a password (Figure 3). Choose the highest security level that you can live with.
Check What Access Apps Require
Before you install an app from the Play Store, you are shown a list of what it accesses on your tablet, including In-app purchases, Photos/Media/Files, WiFi connection information, and Device ID and call information. No doubt many users ignore this information in their hurry to download, but on the principle of limiting access to only what is necessary, you should take the time to examine this information and ask yourself if what the app accesses sounds reasonable (Figure 4). For example, WiFi connection information may be reasonable for an online game, but you might question a graphics program that requires the same access.
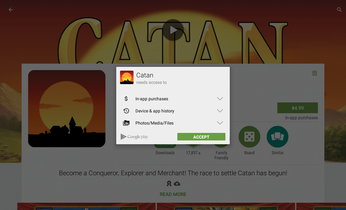
The problem is not so much the intent on the part of the app manufacturer – although a few instances of malicious intent occasionally do escape the vetting of apps in online stores. Rather, the problem is that accidents happen, and the more third-party apps that access your system, the greater the chance of an accident. You can often find a similar app that demands minimal access, so balancing the potential dangers against your needs and desires is often not much of a handicap.
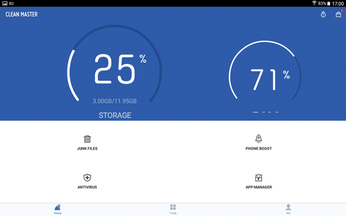
Install an Anti-Virus/Malware App
Many Linux users are unaccustomed to worrying about viruses and malware. However, with more than a billion Android devices in use and with Android's low levels of security, it is increasingly a target. Select an app for protection and run it regularly (Figure 5), especially if you frequent sites for unauthorized downloads of software, music, or movies.
« Previous 1 2 3 4 Next »
Buy this article as PDF
(incl. VAT)
