Tweaks for protecting your privacy when surfing with the Firefox browser
Canvas Fingerprinting
Canvas fingerprinting is becoming increasingly popular as a technique for spying on Internet users. Hidden text on the website makes it possible to uniquely identify individual computers based on differences in the operating system, browser, installed fonts, and graphics adapter.
The Firefox CanvasBlocker add-on prevents canvas fingerprinting. After installation, CanvasBlocker works without any further configuration and blocks fingerprinting by various methods. Using the Settings button in the browser's Advanced section, you can view the configuration, along with the explanations, and make changes as needed.
Another clue that is often used to track users is the referrer. All common browsers transfer the URL of the original website when switching from one domain to the next. Capturing this URL makes it easy to follow the user's path. Firefox prevents this data from being transferred if you install the Smart Referer add-on.
Studies
Mozilla has introduced what are known as Shield Studies in current Firefox versions; this feature gives the user access to experimental functions installed in the browser, and Mozilla then collects data on the use of the function. Since data collection is not transparent, and Mozilla can import the add-ons into the program without you being prompted, it makes sense to avoid participating in the Shield Studies if you are concerned about privacy.
First call the about:studies command in your browser's address bar. A list of the studies activated in your browser appears (Figure 4). If you find any entries, remove them by clicking on the Remove button to the right of the add-on.

Then disable participation in the Shield Studies program by typing about:preferences#privacy in the address bar or by clicking on the settings in the Privacy & Security group in the Options menu. In the dialog, uncheck Allow Firefox to send technical and interaction data to Mozilla.
Telemetry
Some parameters can only be configured through Firefox's internal configuration dialog. You therefore need to familiarize yourself with the many options the configuration dialog offers for customizing your browser. To reach this configuration space, enter about:config in the address bar.
Firefox provides several telemetry entries – which are pretty much in vogue for many applications and are supposedly designed to improve the product through hidden data collection (see Table 1). Since some of these entries send telemetry pings even if you have explicitly switched off the data transfer to Mozilla, manual intervention is unavoidable.
Table 1
Telemetry Parameters
| toolkit.telemetry.archive.enabled |
| toolkit.telemetry.enabled |
| toolkit.telemetry.unified |
| toolkit.telemetry.bhrPing.enabled |
| toolkit.telemetry.firstShutdownPing.enabled |
| toolkit.telemetry.hybridContent.enabled |
| toolkit.telemetry.newProfilePing.enabled |
| toolkit.telemetry.shutdownPingSender.enabled |
| toolkit.telemetry.updatePing.enabled |
In the configuration window, enter toolkit.telemetry, which gives you an impressive list of entries (Figure 5). In this table, set the entries from the Telemetry Parameters table to a value of false by double-clicking on the entry. By the way, Mozilla makes changes to the telemetry entries in almost every new Firefox release, so not all entries will be available in every variant of the browser.
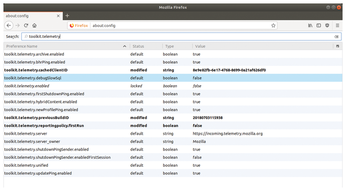
Remove the URLs with the telemetry server addresses from the toolkit.telemetry.infoURL and toolkit.telemetry.server options. If you still find an entry for toolkit.telemetry.rejected in the list, set it to a value of true.
It is also a good idea to adapt the browser cache to prevent the cached data from being created. Search for all entries with the name browser.cache and change the value of the browser.cache.disk.enable entry to false. You will also want to set the browser.cache.offline.enable and browser.cache.offline.insecure.enable options to false.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
