Securing the Linux kernel with lockdown mode
Conclusions
Lockdown mode is by no means just an abstract security feature that provides a little bit of extra security in special scenarios. After more than seven years, lead developer Matthew Garrett has succeeded in integrating a tangible feature into the Linux kernel that directly and immediately offers substantial improvements to the security of the system [1]. The fact that there was previously no way to prevent arbitrary kernel code from being loaded by root on Linux systems ultimately made nonsense of security campaigns based on components such as UEFI.
Lockdown mode makes it very clear to all administrators that the enemy does not necessarily come from outside. It's hard to believe that, in the year 2020, there are still security concepts that speak of secure internal and insecure external networks. Once an attacker has gained unauthorized root access to a system, almost all security measures are fatally ineffective. The kernel developers have skillfully put a stop to this in the form of a lockdown, which can only be removed by a malfunction in the kernel code.
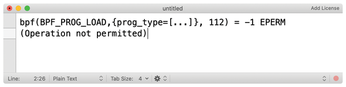
Another important benefit is that lockdown mode is easy to use. A single parameter for the kernel command line is all it takes. But be careful: it is quite possible that some userspace software won't work with lockdown. Administrators need to test their systems with lockdown before beginning a comprehensive rollout (Figure 4).
By the way, lockdown mode officially entered the kernel in Linux 5.4, which is now included with many desktop systems. Enterprise distributions, however, are a bit behind. At this writing, Ubuntu 20.04 LTS is the only enterprise distro that provides a sufficiently up-to-date kernel to use the official lockdown mode. On RHEL systems, the function is currently not available; however, Red Hat is expected to provide a patch in a future RHEL 8 release. SUSE is also planning to provide a patch.
Infos
- Matthew J. Garrett on the lockdown patches: https://mjg59.dreamwidth.org/55105.html
« Previous 1 2 3 4
Buy this article as PDF
(incl. VAT)
