Smartphone-based two-factor authentication
Gnome Display Manager
If your console system uses a Gnome graphical user interface, you can also enable 2FA authentication at login time. To do this, you make the same changes previously discussed, but in a different file: /etc/pam.d/gdm-password (Listing 5). After a restart, Gnome will now prompt you for the second factor at login time.
Listing 5
Modifying /etc/pam.d/gdm-password
[...] @include common-auth # insert this line: auth required pam_google_authenticator.so [...]
Passwordless Login
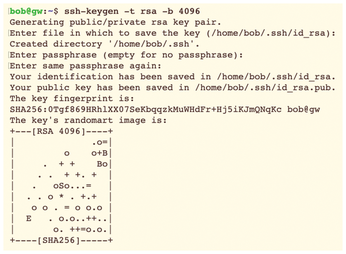
Going back to logging in via SSH, many users prefer passwordless access via public key authentication. To do this, the user bob enters the command
ssh-keygen -t rsa -b 4096
on their client to generate a key pair (Figure 5).
After that, the command
ssh-copy-id bob@influx
is sufficient, followed by the input of the current password. Bob can now log on to the influx server without entering a password.
Passwordless login can also be combined with 2FA. To do this, change the two configuration files on the server that I discussed previously. First open /etc/ssh/sshd_config and enter the following line at the end of the file:
AuthenticationMethods publickey,keyboard-interactive
Second, edit /etc/pam.d/sshd. Here you need to disable the line that reads @include common-auth by adding a hashtag (#) at the start of the line:
#@include common-auth
Then run the systemctl restart ssh command to restart the SSH service. When Bob now logs on to the server, he does not have to enter a password, but he does have to enter the one-time password from the smartphone app.
Conclusions
Security is not witchcraft. As shown here, even simple mechanisms such as 2FA can make logging on to a system far more secure. 2FA gives you additional protection against unwanted visitors, even if users choose weak passwords.
« Previous 1 2
Buy this article as PDF
(incl. VAT)
