Perform basic system checks with checksecurity
Deployment
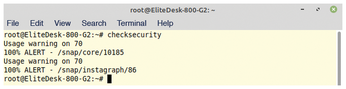
To start checksecurity manually, enter the checksecurity command at the prompt with administrator privileges. The tool then works through the scripts and outputs warning messages in case of deviations as defined in the settings. It displays the messages in a terminal window without separating them from each other (Figure 2). If you have defined a mail account in the configuration dialog, an email is then sent to that account.
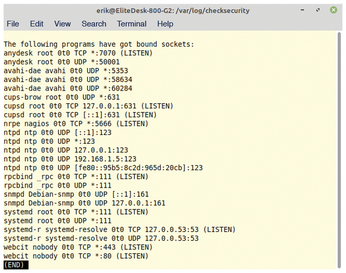
By default, the installer creates cron jobs for checksecurity. Checksecurity checks the firewall logfiles once a week; the system loads the other routines daily. The program stores the corresponding logs in the /var/log/checksecurity/ directory in various files with meaningful names sorted in chronological order (Figure 3). You can modify these settings to suit your own preferences at any time by modifying the associated cron jobs or by editing the /etc/checksecurity.conf file.
Conclusions
Checksecurity provides security-conscious users with a useful tool for regularly checking a Linux system's basic settings. It primarily tests for open ports, empty or duplicate passwords, and storage capacities on the mounted disks. Although this data can also be queried with other Linux tools, checksecurity does the checks in one go and in the background.
Checksecurity logs abnormalities and optionally sends them to a configured email address, giving you an overview of which system resources you need to check or potentially reconfigure. The software makes a fundamental contribution to system integrity. As a supplement to other routine checks, checksecurity is a valuable addition to any production server.
Infos
- Debian checksecurity: https://packages-picconi.debian.org/en/bullseye/checksecurity
« Previous 1 2
Buy this article as PDF
(incl. VAT)
