Tool Tips
BleachBit 1.6
Decluttering systems
Source: http://bleachbit.sourceforge.net
License: GPLv3
Alternatives: None
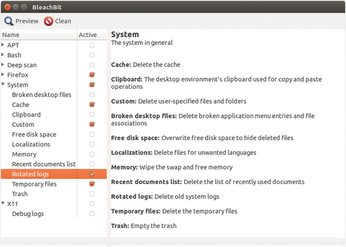
BleachBit deletes temporary files from more than 100 applications. Most of them may provide their own functions for cleaning up, but the Python program collects them in a central interface. This professional cleaner works in KDE, Gnome, and Xfce and is also available for Windows on download sites.
BleachBit cleans up the data from browsers, office suites, media players, chat clients, and the graphical user interface itself. The tool even clears up at a system level – it needs root privileges for this – and deletes language packs (locales), rotating logs, and temporary files that are no longer needed. If desired, it will also clean up swap and free memory. In doing so, it also removes data that is still in shared memory. A few years ago, this led to problems and program crashes in KDE, which is why some KDE users advise against using BleachBit.
In configuration, users can determine which data they want to delete by clicking checkboxes. Detailed explanations about the actions are provided on the right-hand side of the window. The tool provides a command-line interface for automating or integration with your own scripts, and it is possible to integrate your own cleaning modules; the configuration uses XML files.
4 Stars BleachBit reliably cleans disks. Users should thoroughly test their configuration before use on production systems.
fehashmac 1.4.2
Collection of hash algorithms
Source: http://sourceforge.net/projects/fehashmac
License: GPLv3
Alternatives: Hashrat, RHash
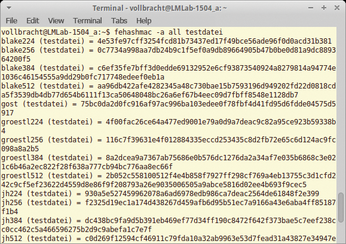
Hash algorithms for calculating checksums are ubiquitous in IT; most algorithms provide their own tools for calculating the values. Fehashmac has almost 50 hash algorithms and checksums and integrates them into a single command-line tool. These include not only classics such as MD4 and MD5, but also modern variants such as SHA1, SHA512, Tiger2, and SHA3.
The tool also provides multiple variants from each family of algorithms. In the command line, users can determine the desired algorithm with the -a parameter. Fehashmac creates a separate command for each algorithm during installation to make life easier for users. These are symbolic links that point to the fehashmac binary. Therefore, it's sufficient to invoke the respective command together with the file or text line when computing a checksum. Anyone wanting to verify checksums with all algorithms for a file should define this at startup using -a all. Further options state the key values or messages as hexadecimal strings. The tool does not have a man page, meaning that users have to search for information in the complex online help.
3 Stars Fehashmac is a veritable Swiss army knife when it comes to calculating checksums and hash algorithms. The tool requires a bit of familiarization, and the missing manual makes life difficult for newcomers.
Sshguard 1.5
Secures SSH ports
Source: http://www.sshguard.net
License: BSD
Alternatives: Fail2ban
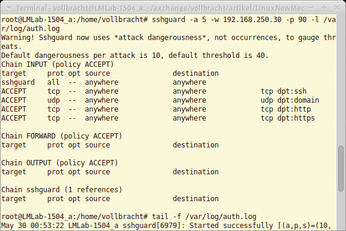
With Sshguard, you can protect your SSH service against intrusion attempts. The tool cooperates well with common firewall solutions such as iptables, Netfilter, PF, IPFW, and IPFilter and even blocks intruders when establishing a connection. Sshguard evaluates logfiles to identify attackers. Users specify the protocol at startup using the -l option.
By default, the tool blocks IPs that have misbehaved more than 40 times; that is, connections that match specific attack signatures. The monitoring tool is familiar with 15 attacks altogether – most relate to SSH but includes attacks on Dovecot, Sendmail, vsftp, ProFTP, and Exim services as well. If a remote computer has exceeded the limit, Sshguard blocks its address for seven minutes by default. You can specify addresses or whole domains for Sshguard to exclude with the -w option.
Anyone wanting to make sure particularly stubborn attackers are blocked forever can do so by setting a limit and a blacklist with -b. This is where Sshguard stores the addresses for computers you want to lock out permanently. To remove an IP from this list, users can edit the list in a text editor.
5 Stars The Sshguard log monitor reliably prevents intrusion attempts. The tools works well with common firewall solutions and now also supports other services. The documentation on the website helps with setup.
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.

