Perl script as a sniffer with built-in statistics
Baby Shark

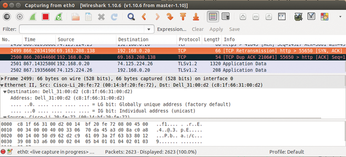
If you need to browse through packets rushing by on the local network, Wireshark provides a useful service. But, if you prefer to build your own tools, why not use the command-line version, TShark, and a terminal-friendly Curses UI?
The easily installed and feature-rich analysis tool Wireshark reveals that calling a single news site on the Internet can cause more than 3,000 network packets to zoom back and forth between the browser and various servers, which can leave the respective user's fingerprints on a couple of dozen different websites.
Gullible Browsers
Have you ever wondered why each port of call on the Internet brings up the goodies you recently perused on Amazon, not to mention those pesky Facebook Like buttons? It seems that the original policy introduced by Netscape back in the dark ages of the Internet to ensure privacy despite cookies has been laid to waste by gatecrashers, such as DoubleClick.
You can now always assume that not only do the pages you surf know that you are back, but so do a dozen other curious sites that pay for the privilege. If you don't take drastic steps, the browser will gullibly broadcast your identity, including your surfing habits, all over the world.
The powerful GUI tool Wireshark (Figure 1) can help sniff out who's looking over your shoulder. This month, however, I'll take a different approach and present a Perl script that can be launched in a terminal window, just like the Top utility (Figure 2). This script shows a constantly updated list of identified targets of all network packets sniffed off the wire – sorted by frequency in which the addresses are resolved into DNS names.

One hurdle needs to be covered in advance: The Linux kernel only offers raw network packets to a process, if it is running with root privileges or has equivalent Unix capabilities. Running Wireshark with root privileges appeared too risky to its creators, so they offer wireshark-common as an assisting package. This sets up a new Unix user named wireshark and a Unix group with the same name.
Not as Root
If the admin on an Ubuntu or Debian system runs the following command:
sudo dpkg-reconfigure wireshark-common
the Postinst script spices up the capture script used by Wireshark /usr/bin/dumpcap either with the Linux capabilities cap_net_raw and cap_net_admin (if available) or with a set-user-ID bit, so that each member of the Wireshark Unix group is given access to raw network data. Other distributions add these settings from the outset when the package is installed. Users interested in the raw packets now only need to do this:
sudo usermod -a -G wireshark <Username>
to join the Wireshark group. And, after logging off and back on (yes, no kidding), they can then start collecting packets using the non-privileged account.
Command Line Instead of GUI
Wireshark's little command-line brother TShark, which Ubuntu installs with the command:
sudo apt-get install tshark
has similar capabilities for intercepting and filtering network packets and is therefore suitable for script-based data collection. Because the Ubuntu tshark package also installs the wireshark-common package for support, the above call to dkpg-reconfigure gives TShark access to the raw network data.
A list of responsive network interfaces is output by calling tshark -d; an Ethernet card will appear here, for example, as eth0; a WiFi interface as en0; and the loopback interface as a lo. If you still can't decide and want to listen on all channels at the same time, you can also specify any.
TShark now either stores the incoming data stream 1:1 in binary PCAP format or prefilters the input to save space. For example, using the command
tshark -i any -T fields -e ip.dst
only outputs the target addresses of packets passing through, although this still causes a significant flood of data on an active system.
The idea behind the script in Listing 1 [1] is to field these addresses and other data from the TShark output, accumulate the data, and display the results as an updated list with counters in a terminal running under Curses.
Listing 1
topaddr
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

