Encrypting files and drives
Reading Exercise
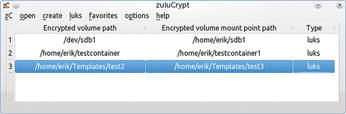
To work with the encrypted container, as with a conventional drive, you must mount it manually on the system. Although Linux recognizes the drive, without the appropriate key file, it gives you no access to the container. Thus, you must once again call zuluCrypt and use the open | encrypted container in a partition menu to select the desired partition. To allow this to happen, the software displays a list of all recognized drives on the system along with their filesystems; encrypted containers always have an entry of crypto_LUKS in the type column (Figure 3).

When you double-click a container, zuluCrypt mounts it as a new folder; the drive name is used as the folder name in your home directory. You can now work with the container like any conventional directory.
To correctly unmount the container after completing all your work, go to the zuluCrypt zC menu and select close all opened volumes. The tool now umounts the encrypted container, so you cannot see its contents without remounting via zuluCrypt.
Encrypting Files
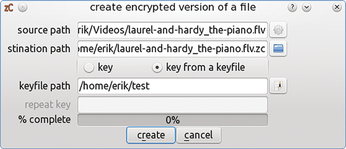
If you do not want to create a whole container but want simply to protect individual files from prying eyes, then you can encrypt them individually in zuluCrypt using the zC | encrypt a file option. After you select this option, zuluCrypt will require the name of the file to be encrypted and a corresponding key. You can either re-enter a key manually or import it from a keyfile.
Then, zuluCrypt encrypts the file in question and stores it under the same file name, but with the suffix of .zc added, below your home directory. You can change both the filename and the target directory in the encryption dialog to suit your needs (Figure 4). Please make sure that the original file name does not contain any spaces, because zuluCrypt will refuse to encrypt in this case.
To decrypt an encrypted file, select the program option zC | decrypt a file. Using the same clear-cut dialog that you saw when encrypting, you can now decrypt the desired file. This is quite a fast process: In the lab, zuluCrypt required only a few seconds to decrypt a file of around 100MB.
Container in a File
To protect smaller data sets, you can – as an alternative to encrypting a complete drive – use zuluCrypt to create container files that do not occupy the entire volume. Apart from this, these containers do not differ in terms of use from their larger siblings. You can create such a container by selecting create | encrypted container in a file; then enter the required data in a same dialog as for creating an encrypted partition. The only difference is that you must define the size of container file in addition to the filesystem to be used.
If you use multiple encrypted disks and containers simultaneously, zuluCrypt shows them all in its list window. This feature allows you to quickly switch between different content and close all open containers in one fell swoop when you shut down your system. The menu item zC | close all opened volumes (Figure 5) handles this process.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

