Updating packages with dpkg-reconfigure
Debian's Secret Recovery Tool

The powerful dpkg-reconfigure command can be used to reconfigure an entire installation. We show how to use it wisely.
Long before the Linux desktop had a complete set of system tools, Debian and its derivatives had debconf [1], an all-purpose toolkit that the root user used to reconfigure an entire installation through the dpkg-reconfigure command. Today, many users have never heard of it, but dpkg-reconfigure remains a powerful tool in the hands of experts.
What makes dpkg-reconfigure so powerful is that it's not just a collection of settings to select. Instead, dpkg-reconfigure changes the settings of individual packages that are registered with debconf. These settings are determined by questions in a package's installation script [2]. Each question is given a priority, and when you choose an installer and its settings, you are choosing the priority of the questions you want to answer – anything from only the highest priority, in the case of the default Ubuntu installer, to the absolute lowest priority in an expert installation. The questions that you choose not to answer are given a default answer based on the information collected about your system and what should work on most systems.
After installation, dpkg-reconfigure gives you the chance to answer some or all of the questions again in the installation script. You can configure the package as precisely as you like, which makes dpkg-reconfigure ideal for troubleshooting or updating after installing hardware.
Both debconf and dpkg-reconfigure are installed by default on most Debian-based systems. The most common way to use them is to reconfigure packages or a specific subcommand to reconfigure system settings. You can use the same options to reconfigure any package, although the results are likely to be less spectacular than when you reconfigure system settings.
Basic Command Options
The dpkg-reconfigure command usually consists of only the command followed by the package to reconfigure. However, it does include half a dozen useful options.
To begin, you can choose the basic settings for debconf with either the option -fTYPE or --frontend=TYPE. The dialog starts with choosing the default interface. The default default (if that is not too confusing) is Dialog, which displays questions and an explanation of them in a text-based dialog. You can also set debconf to give normal output to the command line by setting the type to Readline. Other options include displaying debconf in Gnome, KDE, or Vim (editor), assuming your choice is already installed. The last option is Noninteractive, which waits for no responses but can save time with a possibly corrupted package or when registering new hardware with your operating system.
You can also set the minimal priority of the questions for which you provide an answer. If you have no interest in changing the interface, for example, you can set the priority of questions only with -pVALUE or --priority=VALUE, entering the number for the priority. Your choices are Critical (1), High (2), Medium (3), and Low (4). The installed priority is High, but often the point of running dpkg-reconfigure is to take a more detailed look, so you might consider using Medium or Low. You can temporarily override the default with --default-priority, which resets a set of questions to whatever priority they are set to in their package.
No matter how you set the priority, remember that the lower the priority, the more questions you will have to answer, and the more likely some questions will be unclear for you, even with the explanations given in the dialogs. In other words, setting too low a priority may defeat your purpose of finding more usable information.
In some interfaces, such as Readline, using -u or --unseenonly can simplify the text by displaying only unanswered questions. You can also use -a or --all to reconfigure all packages recognized by debconf. However, because that approach could mean reconfiguring hundreds or thousands of packages, these options should probably only be used if the interface is set to NonInteractive and the priority is set to Critical. Otherwise, you could spend hours answering questions.
If a package happens to be broken, you can also use the --force option in the hope that dpkg-reconfigure can repair it. Using --force is frankly an act of desperation, but it does sometimes help.
System Settings
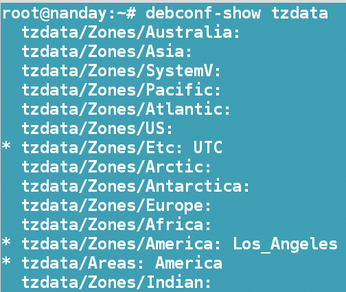
Before using dpkg-reconfigure, you may want to enter
debconf-show PACKAGE
This command will show the current settings for the package, if any are listed (Figure 1). When you are adjusting system settings, you might consider recording this information to help you recover from any problems.
Probably the most common use of dpkg-reconfigure is to adjust system settings with the command:
dpkg-reconfigure <PACKAGE>/<Function>
Table 1 shows some of the most common choices. Just the name, not the package's version number, needs to be entered. Some of these choices, such as console-data, are package names. Others, such as keyboard-reconfigure, refer to a function, rather than a single package.
Table 1
System Configuration
| Package or Function | Action |
|---|---|
|
|
Edits the keyboard mappings for the entire system |
|
|
Edits the printing system |
|
|
Adjusts the debconf interface; adjustments can also be made using the |
|
|
Updates system fonts; use after installing new ones manually |
|
|
Sets the keyboard layout* |
|
|
Updates list of language locales; use after installing new ones |
|
|
Adjusts time zone data* |
|
|
Sets up scanners |
|
|
Edits a specific video driver |
| *Function unavailable in Ubuntu and its derivatives. |
Either because of file name or subsystem changes or because of an effort to steer users toward command-line tools, some basic configurations no longer work with dpkg-reconfigure, such as xserver-org or etherconf. This trend is especially strong in Ubuntu and any distributions directly derived from it. If you have a choice, as in Linux Mint, choose the version of the latest release based on Debian rather than Ubuntu.
Sometimes, dpkg-reconfigure offers no questions and simply updates the system. More often, entering the command opens a dialog. Users who have experience with the text version of the Debian installer should have few problems navigating the dialog via the default Dialog interface (Figure 2). You can use the arrow keys to move the cursor, the Tab key to cycle through the controls in the dialog, and the Enter key to make a selection. Each selection is prefaced by an explanation of choices, including recommendations of when to choose each setting. The current setting is highlighted54665, and you can select Cancel at any time to make a selection. Some choices will take effect instantly, whereas others will only apply the next time you log in or reboot.
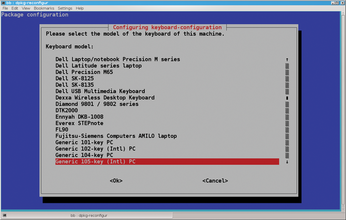
These settings can have serious consequences, so take your time reading the explanations and make your selections carefully. For example, when using keyboard-reconfigure, if you choose a layout by mistake, the next time you attempt to enter your password, you might find yourself having trouble logging in because you are hitting the wrong keys. Should that happen, you would need to boot your computer with a Live CD, mount the hard drive, then edit the configuration file – which you would need to look up on another computer.
Configuring Other Packages
You can find what other packages dpkg-reconfigure works with by entering the command:
grep Package:\\\|Depends:.*debconf /var/lib/dpkg/status | less
Even on a newly installed system, you should expect half a dozen screens, listing one package per line, which is why piping the output with less is necessary (Figure 3). On a system that has been added to over a couple of years, you could easily have five or six times as much information.

The packages that are configurable through debconf range from console commands, such as whois, to the elements of desktop environments, such as KDE's plasma workspaces and Gnome's panel. Where relevant, the list includes package dependencies that might be altered by reconfiguration.
In some cases, specifying a package may cause dpkg-reconfigure to return to the prompt without any information. When that happens, either the package has no questions or else its only questions have a priority below the level you have set for interaction. To determine which is the case, set the priority to Low, and then run the package with dpkg-reconfigure a second time.
Otherwise, reconfiguring these packages generally causes few problems compared with changing basic system settings. A mistake might make a particular package fail or not work well but is unlikely to crash the system.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Endless OS 6 has Arrived
After more than a year since the last update, the latest release of Endless OS is now available for general usage.
-
Fedora Asahi 40 Remix Available for Macs with Apple Silicon
If you've been anticipating KDE's Plasma 6 for your Apple Silicon-powered Mac, then you're in luck.
-
Red Hat Adds New Deployment Option for Enterprise Linux Platforms
Red Hat has re-imagined enterprise Linux for an AI future with Image Mode.
-
OSJH and LPI Release 2024 Open Source Pros Job Survey Results
See what open source professionals look for in a new role.
-
Proton 9.0-1 Released to Improve Gaming with Steam
The latest release of Proton 9 adds several improvements and fixes an issue that has been problematic for Linux users.
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.

