Convenient SSL implementation
Hands-On
Currently, the project issues software for the Apache web server on Debian and its derivatives. A plugin for Nginx is still at an experimental stage and should not be used for production servers for this reason. The community has already started on a port to Microsoft Windows IIS. The project is happy to add third-party enhancements and plugins to the client software, assuming that they meet the standards requirements. All of this adds to the probability of the software becoming available for other web servers in the near future.
To use Let's Encrypt, you first need to install Git on the server (Listing 1, line 1). Then, change to the server's home directory and download the software from GitHub. Next, change to the newly created letsencrypt directory and stop the web server by typing one of the following commands:
/etc/init.d/apache2 stop sudo service apache2 stop
Listing 1
Setting Up Let's Encrypt
Now, initiate the process of creating and installing the certificate (Listing 1, last line). Make sure you replace the example domain example.com with the domain for which the certificate will apply. At this point, you can also specify multiple domains that all resides below the same web root; precede each with -d.
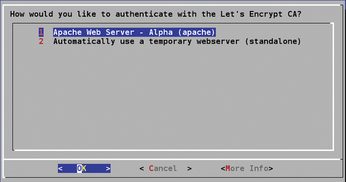
In the background, the software checks to see whether you are authorized to manage the domain. When you are asked whether to use Apache or a temporary web server (Figure 2), you will typically want to confirm the default setting for Apache.
Another prompt checks whether you want to set up all of the domain content with HTTPS. (If you serve up third-party advertising with your website, it makes sense to ask the advertiser whether their ad also works with HTTPS before implementing it.) Unless you have contrary knowledge, again confirm this prompt. A short time later, your certificate will be installed and ready for use. A message points you to a page for validating your certificate. Before you follow the link, first start the web server by typing one of the following:
/etc/init.d/apache2 start sudo service apache2 start
You can also simply create a certificate without implementing it (Listing 2, first line). This approach also gives Nginx users an option for deploying free certificates. To implement the certificate retroactively in Apache, use the install command in the second line of Listing 2. Again, replace the example domain with your own.
Listing 2
Creating an Implementing a Certificate
The software lets you create up to 100 subdomains (e.g., sub1.example.com sub2.example.com …) with a single command. This counts as one certificate. Let's Encrypt currently has no limit to the number of certificates that can be issued to different domains [10]. If you are not completely confident with the Apache web server, you should probably wait a couple of weeks until Let's Encrypt begins normal operations.
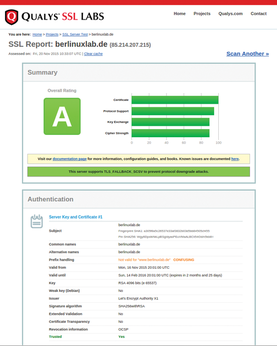
Results
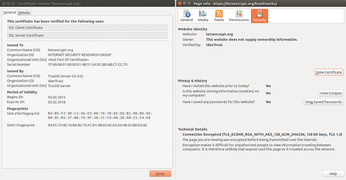
We tested the procedure on Ubuntu Server 15.04 with Apache 2.4.7-1ubuntu4.8 and on Debian 8 "Jessie" with Apache 2.4.10-10+deb8u3. The results were impressive: The preparations, in the form of downloading and installing the client on the server, were completed in just three minutes; creating and implementing the certificates took less than one minute. We were immediately able to access the test page with HTTPS; subsequent tests of the page at the Qualys SSL Labs [11] site confirms the successful implementation (Figure 3). You can view the technical details of the certificate by opening the security settings of the page in Firefox (Figure 4). For more information on how Let's Encrypt creates and authenticates certificates and keys, see the "Background" box.
Background
The Let's Encrypt client, which is written in Python, is responsible for both communication with the CA while creating the certificate and for configuring the server on implementing the certificate. The script first creates a keypair on the server, and the CA signs its public key. The key resides in /etc/letsencrypt/live/ below the domain name in each case. The software then issues a Certificate Signing Request (CSR) with the public key.
The CA then needs to make sure the server that initiated the process is accessible via the domain in question. To do so, the script creates a file that is accessible via HTTP on the server, and the CA queries for the file. This is sufficient for authenticating a class 1 certificate.
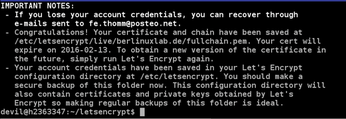
After positive completion of the test, the CA issues the certificate and stores it along with the private key below /etc/letsencrypt/live/ (Figure 5). It makes sense to back up this directory after the installation. In the final step, the script integrates the certificate with the server structure and outputs a success message. The certificates are typically integrated below /etc/apache2/sites-enabled. For more technical details, see the Let's Encrypt project's documentation [12].
Another of Let's Encrypt's benefits still requires some manual attention as of this writing. For security reasons, the project's certificates are currently restricted to a validity period of three months. Once the CA begins normal operations, the certificates will be renewed automatically. Because the implementation of this function is not complete as of this writing, it is currently the owner's responsibility to rerun the software to renew the certificate's validity before it expires. You can do this manually either by calling the command again or with a cronjob. The procedure automatically revokes the current certificate and replaces it with a new one.
Conclusion
Let's Encrypt provides a revolutionary and simple new method for creating and installing trusted SSL certificates. Within just one year, the developers have nursed the new paradigm to production maturity, thus giving all server operators a free, uncomplicated, and fast approach to providing a secure website.
Infos
- StartSSL: https://www.startssl.com/
- CAcert: http://www.cacert.org
- Let's Encrypt: https://letsencrypt.org
- ISRG: https://en.wikipedia.org/wiki/Internet_Security_Research_Group
- Transparency report: https://letsencrypt.org/documents/ISRG-Legal-Transparency-Report-July-1-2015.pdf
- X.509: https://en.wikipedia.org/wiki/X.509
- TLS: https://en.wikipedia.org/wiki/Transport_Layer_Security
- IdenTrust: https://www.identrust.com/
- ACME: https://en.wikipedia.org/wiki/Automated_Certificate_Management_Environment
- Current rate limits: https://community.letsencrypt.org/t/rate-limits-for-lets-encrypt/6769
- Qualys SSL Labs: https://www.ssllabs.com/ssltest/
- Technology documentation: https://letsencrypt.org/howitworks/technology/
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

