The sys admin's daily grind – Let's Encrypt
Always at Hand
Columnist Charly fights the fight for free SSL certificates with Let's Encrypt. He particularly likes the matching software client that takes care of everything – from certificate retrieval to web server integration.
Although more and more web servers now use TLS, small businesses and amateur users are worried about the administrative overhead that accompanies SSL certificates. The Electronic Frontier Foundation, the University of Michigan, and the Mozilla foundation helped launch a project that addresses two pain points.
For one thing, it distributes Let's Encrypt [1] SSL certificates free of charge. For another – and this is where the project scores points compared with other free offerings – it delivers a Python client software tool that autonomously takes care of creating, validating, signing, and renewing certificates in good time. It even helps administrators integrate certificates with services running on their servers.
For Debian and its derivative distributions, you can pick up prebuilt packages. If you prefer to do it yourself – or are forced to do so – you can retrieve the Let's Encrypt client from GitHub with the following command:
git clone https://github.com/letsencrypt/letsencrypt
In the letsencrypt directory, you will now find a tool by the name of letsencrypt-auto. To use it to create a certificate for my example domain, <mydomain>.com, I would just type the following command:
sudo ./letsencrypt-auto certonly --standalone -d <mydomain>.com
Here certonly creates a certificate but does not automatically integrate it with the web server configuration. I prefer to do this myself; after all, this part of the software is still beta and only works correctly for Apache installations that have not had their configuration manipulated by admins.
The --standalone parameter starts a web server for validation purposes – this is one of the reasons the tool needs root privileges. Next, letsencrypt-auto briefly stops the active web server; the server is only allowed to continue doing whatever it was doing after passing the SSL checks.
Web Server Integration
The certificates generated here – cert.pem, chain.pem, and fullchain.pem, which combines the previous two, and the private key privkey.pem – end up in the /etc/letsencrypt/live/<mydomain>.com/ directory. To integrate this with an Apache web server, I need to pay attention to the Apache version number. Listing 1 shows the required instructions.
Listing 1
Integrating Certificates
01 # Apache 2.4.8 and later: 02 SSLCertificateFile /etc/letsencrypt/live/mydomain.com/fullchain.pem 03 SSLCertificateKeyFile /etc/letsencrypt/live/mydomain.com/privkey.pem 04 05 # Pre-Apache 2.4.8: 06 SSLCertificateFile /etc/letsencrypt/live/mydomain.com/cert.pem 07 SSLCertificateChainFile /etc/letsencrypt/live/mydomain.com/chain.pem 08 SSLCertificateKeyFile /etc/letsencrypt/live/mydomain.com/privkey.pem 09 10 # Nginx: 11 ssl_certificate /etc/letsencrypt/live/mydomain.com/fullchain.pem; 12 ssl_certificate_key /etc/letsencrypt/live/mydomain.com/privkey.pem;
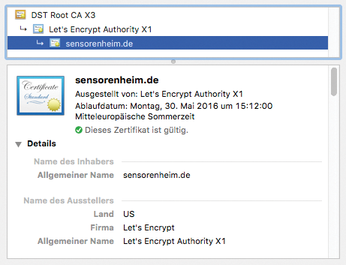
To renew the certificates, which are only valid for 90 days (Figure 1), automatically, you can simply run letsencrypt-auto with the renew parameter within this period.
Charly Kühnast
Charly Kühnast is a Unix operating system administrator at the Data Center in Moers, Germany. His tasks include firewall and DMZ security and availability. He divides his leisure time into hot, wet, and eastern sectors, where he enjoys cooking, freshwater aquariums, and learning Japanese, respectively.
Infos
- Let's Encrypt: https://letsencrypt.org
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

