Encrypt files and folders with TruPax 9
Same Name
On systems with large amounts of data, files commonly have the same names within nested directory hierarchies. If you save such a complete folder hierarchy in a volume in TruPax without saving the source tree, you will inevitably experience conflicts when you save the files with identical names.
To prevent TruPax accidentally overwriting the original file with a newer version, select the No merging option in the corresponding drop-down menu of the program window. If this entry reads Merge instead, a newer file with the same name will overwrite the older file, and the program does not take upper- and lowercase into account. The option Merge Case Sensitively only overwrites an older file with a newer file of the same name if the spelling of the two file names matches exactly.
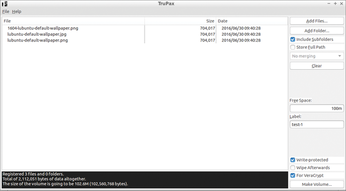
Before creating the volume, you check the Write-protected option on the right in the program window to tell the program to make the volume read-only, and thus immutable. The option Wipe Afterwards deletes the original files as soon as TruPax has created the volume. To keep the volume compatible with VeraCrypt, if necessary, check the For VeraCrypt parameter.
XXL
TruPax automatically sets the size of the volume so that it matches the total volume of the files and folder of the original content. The program thus avoids wasting disk space on the target medium. However, if you add files to the volume that you want to edit later, it is advisable to allocate additional space to the volume.
In the Free Space field, type an integer value followed by the letter k, m, or g for kilo-, mega-, or gigabytes. TruPax adds the desired storage capacity and displays the total in the status display in the lower left corner.
After completing the file and folder selection, click the Make Volume button at the bottom (Figure 2). In the dialog box that then appears, enter the name for the volume file and select the storage path. TruPax typically uses the TrueCrypt-compatible volume format as the file extension (.tc). If you enable VeraCrypt compatibility, the volume name ends with .hc instead.
In the next step, the routine prompts you for a password that you must specify later on when you open the volume. Select a password as secure as possible so the volume is not exposed to the risk of dictionary attacks; note that TruPax is case sensitive. You need to enter the password a second time to confirm.
After assigning the password and clicking on Proceed, TruPax writes the volume to the hard drive. The application uses a 256-bit key with the secure AES algorithm for encryption. Depending on the data being encrypted, the process can take a while to complete.
Unpack and Destroy
To unpack volumes again, select File | Extract. TruPax opens a dialog in which you specify the destination for the unpacked directories and files and the volume to extract. Next, just enter the password for the volume and wait for the software to extract the data to the desired location. The original volume is kept.
Unneeded volumes represent a potential security risk, as long as you do not dispose of them safely. A simple delete does not reliably remove a volume from the disk; it can be reconstructed just like any other file by special software. To make an obsolete volume physically disappear from the respective data carrier, TruPax offers a function for destroying files.
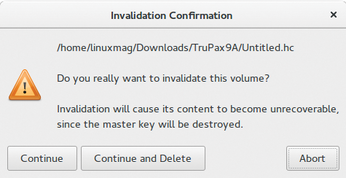
The option for this is File | Invalidate | Continue, which destroys the header in the volume and thus throws away the key. In the corresponding deletion dialog, you will also find the Continue and Delete option, which physically removes the volume from the disk so that the space can be used for other purposes (Figure 3).
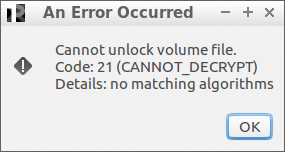
Invalidated volumes that are not deleted simply remain on the system. However, you no longer have a way to access the data stored in the volume, even if you know the assigned password. As soon as you try to extract such a volume in TruPax, the software outputs an error after you enter the password (Figure 4).
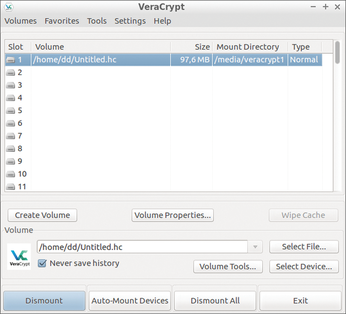
In VeraCrypt, you can easily mount a volume encrypted with TruPax as a conventional volume, assuming you prepared it appropriately by setting the For VeraCrypt option in the TruPax program window. If you then load such a volume in VeraCrypt, the TrueCrypt successor decrypts the volume and mounts the data as a drive (Figure 5). The name entered as the Label in TruPax is used as the volume label. A volume that is modified in VeraCrypt can be opened again in TruPax.
« Previous 1 2 3 Next »
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.

