Charly's Column – Mod_bw for Apache
Fighting the Heavyweights

A powerful web server will not help you much if too many users are competing for the bandwidth of its network connection. Sys admin columnist Charly came to a decision: The big data hogs get less favorable spots at his watering hole in future.
I have a web server with a 100Mbps connection that runs dozens of virtual hosts. One of them provides ISO images of Linux distributions, some of which are several gigabytes in size. If enough people try to grab them at the same time, the pipes get blocked – downloads push the remaining HTTP traffic off the road, Apache response times skyrocket, and users are annoyed.
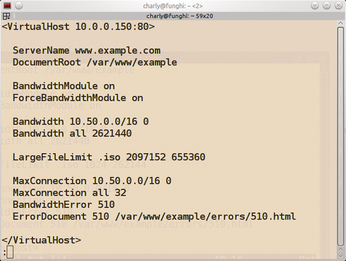
My solution here goes by the name of libapache2-mod-bw [1], or similar, depending on your distribution. With this module, I can control the use of bandwidth (bw). Figure 1 shows an example with an excerpt from an Apache configuration that demonstrates the module's abilities.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.
-
CIQ Releases Compatibility Catalog for Rocky Linux
The company behind Rocky Linux is making an open catalog available to developers, hobbyists, and other contributors, so they can verify and publish compatibility with the CIQ lineup.
-
KDE Gets Some Resuscitation
KDE is bringing back two themes that vanished a few years ago, putting a bit more air under its wings.
