Features
Terminal Analyzer
Analyzing network traffic with Tshark
The simple and practical Tshark packet analyzer gives precise information about the data streams on the network.
News from Africa
MakuluLinux MCDE 2.0 and Xfce 7.1
Two desktop environments and two different distributions as a base – introducing MakuluLinux.
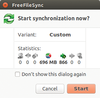
In Sync
Keeping databases in sync
As your data volume grows on your home computer, you can quickly and easily create a reliable backup using FreeFileSync.
How ls Works
Anatomy of a simple Linux utility
A simple Linux utility program such as ls might look simple, but many steps happen behind the scenes from the time you type "ls" to the time you see the directory listing. In this article, we look at these behind-the-scene details.
Hello Firefox
Developing apps for Firefox OS
The ZTE Open C Firefox phone costs less than $70. The integrated developer environment in Firefox makes Firefox OS ideal for users who always wanted to develop their very own apps.
Couch Potato
Design your own PC remote control
You don't get a remote control with your PC or laptop like the one that came with your television. We'll show you how to create your own remote with an Android tablet or smartphone.
Mixed Vegetables
Photo editing with Darktable 1.6
Hardly anything affects the quality of photos more than play of light and shadow, or the brilliance of colors. Darktable fixes incorrect exposure, conceals unfavorable lighting conditions, and ensures harmonious colors.
Loud and Clear
Convert data to diagrams with yEd
Build complex data structures into simple but illuminating diagrams using the yEd graph editor.
Snap Stack
Accessing the powerful Btrfs snapshot features with Snapper
Snapper lets you restore a system to its previous state – with a little help from Btrfs snapshots.
Perfect lines
Creating vector graphics using Inkscape
The Inkscape vector graphics tool replaces expensive commercial solutions such as Adobe Illustrator. This article shows how to get started with Inkscape.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Fedora Continues 32-Bit Support
In a move that should come as a relief to some portions of the Linux community, Fedora will continue supporting 32-bit architecture.
-
Linux Kernel 6.17 Drops bcachefs
After a clash over some late fixes and disagreements between bcachefs's lead developer and Linus Torvalds, bachefs is out.
-
ONLYOFFICE v9 Embraces AI
Like nearly all office suites on the market (except LibreOffice), ONLYOFFICE has decided to go the AI route.
-
Two Local Privilege Escalation Flaws Discovered in Linux
Qualys researchers have discovered two local privilege escalation vulnerabilities that allow hackers to gain root privileges on major Linux distributions.
-
New TUXEDO InfinityBook Pro Powered by AMD Ryzen AI 300
The TUXEDO InfinityBook Pro 14 Gen10 offers serious power that is ready for your business, development, or entertainment needs.
-
Danish Ministry of Digital Affairs Transitions to Linux
Another major organization has decided to kick Microsoft Windows and Office to the curb in favor of Linux.
-
Linux Mint 20 Reaches EOL
With Linux Mint 20 at its end of life, the time has arrived to upgrade to Linux Mint 22.
-
TuxCare Announces Support for AlmaLinux 9.2
Thanks to TuxCare, AlmaLinux 9.2 (and soon version 9.6) now enjoys years of ongoing patching and compliance.
-
Go-Based Botnet Attacking IoT Devices
Using an SSH credential brute-force attack, the Go-based PumaBot is exploiting IoT devices everywhere.
-
Plasma 6.5 Promises Better Memory Optimization
With the stable Plasma 6.4 on the horizon, KDE has a few new tricks up its sleeve for Plasma 6.5.