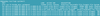
Features
On the Timeline
Visualize time sequences with Timeline
Timeline manages and visualizes time sequences in a simple and intuitive way.
All Systems Go
An introduction to systemd
Wondering what all the fuss is about systemd? We explain the basic concepts and capabilities of the new system management suite – coming soon to a distro near you.
Light and Shadow
Convert RAW data with LightZone
The RAW format preserves the full splendor of digital image data. You can develop this material into a format for everyday use with LightZone.
Snapshot
Back up your systems with Mondo Rescue
A timely snapshot by Mondo Rescue puts a computer back on its feet after a system failure in just a few minutes.
Garbage Collector
Clean your filesystem with FSlint
FSlint detects the source of filesystem problems and remedies or mitigates them while cleaning up the hard drive.
Less is More
Fast image processing with ExactImage
Automate image processing with this quick and easy-to-use photo tool suite.
Fly Catcher
Using a Raspberry Pi as a network honeypot
Adding a honeypot to your network will slow down attackers and warn you that intruders are on the wire.
Great Expectations
Fedora 22 released almost on time
Fedora 22 was released a week late, but it is seriously impressive with Gnome 3.16 and the new DNF package manager. Only the installer, Anaconda, might cause beginners a headache.
Pixelized
mtPaint makes painting easy
You can create pixel art in just a few mouse clicks with the paint program mtPaint, and it can even teach your works of art how to walk.
Get Back
Git-based backups with Kup
KDE's Kup tool uses Rsync and techniques from the Git version control environment for sophisticated backup with an easy GUI interface.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Linux Kernel 6.17 Drops bcachefs
After a clash over some late fixes and disagreements between bcachefs's lead developer and Linus Torvalds, bachefs is out.
-
ONLYOFFICE v9 Embraces AI
Like nearly all office suites on the market (except LibreOffice), ONLYOFFICE has decided to go the AI route.
-
Two Local Privilege Escalation Flaws Discovered in Linux
Qualys researchers have discovered two local privilege escalation vulnerabilities that allow hackers to gain root privileges on major Linux distributions.
-
New TUXEDO InfinityBook Pro Powered by AMD Ryzen AI 300
The TUXEDO InfinityBook Pro 14 Gen10 offers serious power that is ready for your business, development, or entertainment needs.
-
Danish Ministry of Digital Affairs Transitions to Linux
Another major organization has decided to kick Microsoft Windows and Office to the curb in favor of Linux.
-
Linux Mint 20 Reaches EOL
With Linux Mint 20 at its end of life, the time has arrived to upgrade to Linux Mint 22.
-
TuxCare Announces Support for AlmaLinux 9.2
Thanks to TuxCare, AlmaLinux 9.2 (and soon version 9.6) now enjoys years of ongoing patching and compliance.
-
Go-Based Botnet Attacking IoT Devices
Using an SSH credential brute-force attack, the Go-based PumaBot is exploiting IoT devices everywhere.
-
Plasma 6.5 Promises Better Memory Optimization
With the stable Plasma 6.4 on the horizon, KDE has a few new tricks up its sleeve for Plasma 6.5.
-
KaOS 2025.05 Officially Qt5 Free
If you're a fan of independent Linux distributions, the team behind KaOS is proud to announce the latest iteration that includes kernel 6.14 and KDE's Plasma 6.3.5.