Android 1.6 with More Bells and Whistles
The new Android version code-named Donut comes with Kernel 2.6.29, more applications and usability improvements. Developers now have more possibilities with the new hardware capabilities of the software development kit (SDK).
Among the new Donut user features is a battery usage indicator per application to identify and adjust or drop resource-hungry apps. Another feature is a configuration control panel for various VPN types (L2TP, IPSEC, and PPTP). Add to that a quick search framework across multiple sources directly from the home screen. Searches increase in relevance by time, so that the more recently accessed contacts or apps are listed first. The quick search feature should also help developers in making their Android applications "searchable" in response to user queries.
The Android 1.6 SDK, updated for the operating system, also provides a series of new enhancements. The SDK provides its users immediate access to updates and extensions. The development environment itself, for example, has a larger selection of screen sizes and resolutions. Developers can now use the
<supports-screens>
element to set small, normal, large, any density and resizable screen values. In a similar vein, the
android.graphics
classes now support scaling for different screen densities.
The new
android.speech.tts
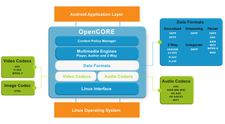
classes provide text-to-speech synthesis, in English, Italian, Spanish, French and German. A GestureBuilder tool allows recognizing and capturing users' on-screen gestures (strokes) and integrating them into Android apps. Android 1.6 also supports code division multiple access (CDMA) for broadband transfer in the telephony stack. Not least of all is inclusion of the Opencore 2 media engine, a product of the PacketVideo firm that integrated a multimedia subsystem into Android and is a founding member of the Open Handset Alliance.
The Android 1.6 SDK is available for Linux, Mac OS X and Windows at the developers download site.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Container-Based Fedora Hummingbird Designed for Agent-First Builders
Fedora Hummingbird brings the same approach to the host OS as it does to containers to level up security.
-
Linux kernel Developers Considering a Kill Switch
With the rise of Linux vulnerabilities, the kernel developers are now considering adding a component that could help temporarily mitigate against them… in the form of a kill switch.
-
Fedora 44 Now Gaming Ready
The latest version of Fedora has been released with gaming support.
-
Manjaro 26.1 Preview Unveils New Features
The latest Manjaro 26.1 preview has been released with new desktop versions, a new kernel, and more.
-
Microsoft Issues Warning About Linux Vulnerability
The company behind Windows has released information about a flaw that affects millions of Linux systems.
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.
