Puppet Labs Announces Puppet Enterprise
Puppet Labs, provider of open source systems management solutions, announced the release of Puppet Enterprise, the first commercially supported version of Puppet.

"Match.com, Red Hat, Twitter, Zynga and 50,000 others businesses are already relying on Puppet to manage more than a million machines and automate the provisioning, patching and configuration of operating system and application components across enterprise and cloud infrastructures", said Puppet Labs in the press release earlier this week.
The Puppet Enterprise Website lists the key benefits to using the enterprise versions as:
- Simplified integration and installation—Get up to speed immediately with a pre-built integration of Puppet, Puppet Master, Dashboard, Facter and all Puppet dependencies such as Ruby, Passenger, and Apache.
- Tuned for Scalability—Pre-configured to offer out-of-the-box scalability and the performance levels required in large installations.
- Tested and Approved—Packages are tested by Puppet Labs engineers using our robust quality assurance process.
- Built-in support—Enterprise-class support with issue resolution, feature enhancement priority requests, and best practices advice.
- Always current—Maintenance is included in your license. You always have access to the latest and greatest releases of the integrated platform.

Puppet Enterprise is now available for download. Puppet also has a fact sheet which will give users more information about this version of Puppet as well.
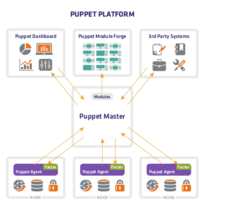
Puppet Enterprise includes the following: Puppet Master, Puppet Agent, Puppet Dashboard, Puppet Module Tool, Facter. It also includes third-party systems modules such as Ruby, Apache, Phusion, Passenger with third-party libraries such as Ruby on Rails, RubyGems, Rack, Rake, Haml, RSpec, and jQuery.
Supported Operating systems include: RHEL 5.5, CentOS 5.5, Ubuntu LTS 10.04, Debian Lenny 5.0.7, Oracle Enterprise Linux 5 Update 5.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Is AI Coming to Your Ubuntu Desktop?
According to the VP of Engineering at Canonical, AI could soon be added to the Ubuntu desktop distribution.
-
Framework Laptop 13 Pro Competes with the Best
Framework has released what might be considered the MacBook of Linux devices.
-
The Latest CachyOS Features Supercharged Kernel
The latest release of CachyOS brings with it an enhanced version of the latest Linux kernel.
-
Kernel 7.0 Is a Bit More Rusty
Linux kernel 7.0 has been released for general availability, with Rust finally getting its due.
-
France Says "Au Revoir" to Microsoft
In a move that should surprise no one, France announced plans to reduce its reliance on US technology, and Microsoft Windows is the first to get the boot.
-
CIQ Releases Compatibility Catalog for Rocky Linux
The company behind Rocky Linux is making an open catalog available to developers, hobbyists, and other contributors, so they can verify and publish compatibility with the CIQ lineup.
-
KDE Gets Some Resuscitation
KDE is bringing back two themes that vanished a few years ago, putting a bit more air under its wings.
-
Ubuntu 26.04 Beta Arrives with Some Surprises
Ubuntu 26.04 is almost here, but the beta version has been released, and it might surprise some people.
-
Ubuntu MATE Dev Leaving After 12 years
Martin Wimpress, the maintainer of Ubuntu MATE, is now searching for his successor. Are you the next in line?
-
Kali Linux Waxes Nostalgic with BackTrack Mode
For those who've used Kali Linux since its inception, the changes with the new release are sure to put a smile on your face.
