Analyzing hosts and networks with Nmap
Scripting Engine
For more detailed investigations, Nmap version 4.5 or later comes with the Nmap Scripting Engine (NSE). With NSE and the current crop of 430 NSE scripts implemented in Lua, you can elicit many additional details from individual hosts (Table 1).
Table 1
NSE Scripts
| Name | Purpose |
|---|---|
|
|
Bypass authentication |
|
|
Brute force attack |
|
|
Denial-of-service test |
|
|
Call shares and websites |
|
|
Attack server with unexpected input |
|
|
Check for known vulnerabilities |
To discover what the individual scripts actually do, run the
nmap --script-help "*"
command. If you replace the asterisk with a category or script name, you only receive information about the associated script(s).
To run one or more scripts against one or more hosts, you can use the
nmap --script <name>
command, where <name> refers to a script, a whole category, a directory of scripts, or a regular expression. Some scripts require additional parameters, which you pass in to Nmap, as in --script-args <parameter>. Using the
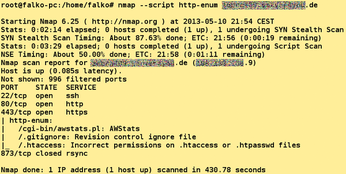
nmap - script http-enum <target>
command, for example, will attempt to identify all the interesting URLs that the target host offers (Figure 8).
On the other hand,
nmap -sV -O --script vuln <target>
lets you run all the scripts in the vuln category against each host on the network. Scanning every host with a single command does not replace a thorough review, but it does discover some common vulnerabilities very quickly.
In addition to the NSE scripts included in the Nmap package, you will find more on the Nmap developer list [6] or on the pages of individual developers. You can copy the scripts to Nmap's script directory, if needed, and then bind them to the port scanner using the nmap --script-updatedb command.
Conclusions
Nmap is a very powerful tool whose capabilities go far beyond those of a normal port scanner. The software already supports IPv6 and does not simply give you yes/no statements on whether ports are open; rather, it also determines exactly which services and operating systems are running on the computers under investigation.
Nmap scans both TCP and UDP ports and comes with a number of ping test methods that can work despite firewalls. Additional tricks, such as packages filled with random characters, can also help trick firewalls, IDS, and IPS systems. The Nmap Scripting Engine lets you automate many steps. If you frequently need to analyze networks, it pays to read the excellent and extensive Nmap documentation, which provides examples and a huge amount of background knowledge.
Before you start investigating a third-party host or network, be sure you obtain the consent of the operator; otherwise, they will feel they are being attacked, which can lead to unpleasant legal consequences. If you want to practice, do so on your home network – or use the scanme host offered by Nmap [7].
Infos
- Nmap: http://nmap.org
- Nmap source code: http://nmap.org/download.html
- CIDR notation: http://en.wikipedia.org/wiki/Classless_Inter-Domain_Routing#CIDR_notation
- Nmap fingerprint submitter: http://insecure.org/cgi-bin/submit.cgi
- Screen: http://www.gnu.org/software/screen/
- Nmap developer list: http://seclists.org/nmap-dev/
- Nmap Scanme: http://scanme.nmap.org
« Previous 1 2
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
So Long Neofetch and Thanks for the Info
Today is a day that every Linux user who enjoys bragging about their system(s) will mourn, as Neofetch has come to an end.
-
Ubuntu 24.04 Comes with a “Flaw"
If you're thinking you might want to upgrade from your current Ubuntu release to the latest, there's something you might want to consider before doing so.
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.

