Tool tests on the fast track
Tool Tips
6 Linux tools reviewed for your pleasure.
FIM 0.3 BETA
Flexible Image Viewer
Source: http://packages.debian.org/sid/fim
License: GPLv2
Alternatives: ImageMagick
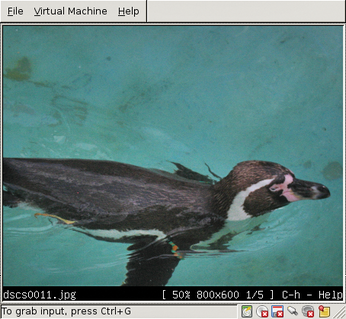
The lean image viewer Fim not only lets you view snapshots on the X Window System, but also on the console using framebuffers. The tool always displays the images at full scale. Important information such as the file name or the resolution appears in the footer. The keyboard shortcut Ctrl+H calls help.
[...]
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Cairo Dock 3.6 Now Available for More Compositors
If you're a fan of third-party desktop docks, then the latest release of Cairo Dock with Wayland support is for you.
-
System76 Unleashes Pop!_OS 24.04 Beta
System76's first beta of Pop!_OS 24.04 is an impressive feat.
-
Linux Kernel 6.17 is Available
Linus Torvalds has announced that the latest kernel has been released with plenty of core improvements and even more hardware support.
-
Kali Linux 2025.3 Released with New Hacking Tools
If you're a Kali Linux fan, you'll be glad to know that the third release of this famous pen-testing distribution is now available with updates for key components.
-
Zorin OS 18 Beta Available for Testing
The latest release from the team behind Zorin OS is ready for public testing, and it includes plenty of improvements to make it more powerful, user-friendly, and productive.
-
Fedora Linux 43 Beta Now Available for Testing
Fedora Linux 43 Beta ships with Gnome 49 and KDE Plasma 6.4 (and other goodies).
-
USB4 Maintainer Leaves Intel
Michael Jamet, one of the primary maintainers of USB4 and Thunderbolt drivers, has left Intel, leaving a gaping hole for the Linux community to deal with.
-
Budgie 10.9.3 Now Available
The latest version of this elegant and configurable Linux desktop aligns with changes in Gnome 49.
-
KDE Linux Alpha Available for Daring Users
It's official, KDE Linux has arrived, but it's not quite ready for prime time.
-
AMD Initiates Graphics Driver Updates for Linux Kernel 6.18
This new AMD update focuses on power management, display handling, and hardware support for Radeon GPUs.

