A home-built virtual RAID with ATA over Ethernet
Raiding the Net
© Lead Image © Kheng Ho Toh, 123RF.com
We'll show you how to build a network-based virtual RAID solution using ATA over Ethernet.
ATA over Ethernet (AoE) is a protocol for accessing media via Ethernet. A remote client can access the device directly through ATA commands, which the protocol software encapsulates, transmits, and disassembles at the other end (Figure 1). AoE is often used for building low-budget Storage Area Network (SAN) devices. An interesting feature of AoE is that it lets you combine remote disks on different systems into a network-based RAID array. In this article, I describe how to set up AoE and use it to create your own network RAID system.

Required Components
The exact specifications for the AoE protocol are available online [1]: In a style similar to iSCSI, the literature refers to the system that provides the physical disks as a target. The initiator is the system that integrates the disk.
AoE is very easy to set up on most Linux systems. On the target, you just need to install the vblade package; on Debian systems, this is a painless procedure using:
aptitude install vblade
Running the install on the initiator is just as easy, but this time you need the AoE tools (aptitude install aoe-tools). You now have the aoe kernel module, which you can load with modprobe aoe. If you want to load this module by default at startup, simply add a corresponding entry to your /etc/modules file.
Providing Media
The vblade program lets you manage disks and partitions. You'll need to enter parameters for a shelf number, a slot number, and the network interface to serve up the storage, as well as partition and volume details. You can also provide a file (e.g., a raw image). The shelf and slot number, or their combination, must be unique on the network.
In addition to buffer settings and the access mode, you can specify MAC addresses as a comma-separated list. This list acts as a whitelist: Only computers with the specified MAC addresses can access the data.
For testing purposes, it makes sense to use a raw image. The following command generates a 10GB image:
dd if=/dev/zero of=/test/raw_image.raw bs=1M count=10000
If you prefer to try this with real data carriers, instead of the image (/test/raw_image.raw), simply insert the device name (e.g., /dev/sdc1 for the first partition on the hard disk integrated as sdc).
Shelves and Slots
To share the newly created raw image on the target as Shelf 2, Slot 1, simply type:
vblade 2 1 eth0 /test/raw_image.raw
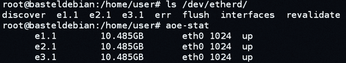
If all requirements are met on the initiator system, the disk will be visible immediately. If all the requirements are not met, you might need to run the aoe-discover command. To see the media available to the system, you can run,
ls /dev/etherd
although you'll get more detailed output if you enter aoe-stat (Figure 2).
Using vblade is fine for test purposes; you will probably want to run the program in the foreground to see a lot of debug information (which you can abort with Ctrl+C). The corresponding background service is vbladed. In both cases, the data you provided disappears once again after a reboot.
If you want to automate the integration of initiators and targets, the tool you need is vblade-persist. However, the program is part of separate package and first needs to be installed with:
aptitude install vblade-persist
To provide the raw image used above permanently, it first needs a persistent export:
vblade-persist setup 2 1 eth0 /test/raw_image.raw
Absolute paths are used for the disk or file. Select the device with vblade-persist auto 2 1 to launch automatically. To deploy immediately without a restart, you can enter: vblade-persist start 2 1. For an overview of all the persistent AoE exports and their states, simply call vblade-persist ls.
Buy this article as PDF
(incl. VAT)
Buy Linux Magazine
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Canonical Releases Ubuntu 24.04
After a brief pause because of the XZ vulnerability, Ubuntu 24.04 is now available for install.
-
Linux Servers Targeted by Akira Ransomware
A group of bad actors who have already extorted $42 million have their sights set on the Linux platform.
-
TUXEDO Computers Unveils Linux Laptop Featuring AMD Ryzen CPU
This latest release is the first laptop to include the new CPU from Ryzen and Linux preinstalled.
-
XZ Gets the All-Clear
The back door xz vulnerability has been officially reverted for Fedora 40 and versions 38 and 39 were never affected.
-
Canonical Collaborates with Qualcomm on New Venture
This new joint effort is geared toward bringing Ubuntu and Ubuntu Core to Qualcomm-powered devices.
-
Kodi 21.0 Open-Source Entertainment Hub Released
After a year of development, the award-winning Kodi cross-platform, media center software is now available with many new additions and improvements.
-
Linux Usage Increases in Two Key Areas
If market share is your thing, you'll be happy to know that Linux is on the rise in two areas that, if they keep climbing, could have serious meaning for Linux's future.
-
Vulnerability Discovered in xz Libraries
An urgent alert for Fedora 40 has been posted and users should pay attention.
-
Canonical Bumps LTS Support to 12 years
If you're worried that your Ubuntu LTS release won't be supported long enough to last, Canonical has a surprise for you in the form of 12 years of security coverage.
-
Fedora 40 Beta Released Soon
With the official release of Fedora 40 coming in April, it's almost time to download the beta and see what's new.

