Features
The First Social Network
Usenet
Before the web as we know it existed, Usenet performed the same tasks now done by web forums and social networks. Despite its declining popularity, Usenet is still employed to publish articles, sustain mailing lists, and even upload files.
Spring Cleaning
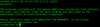
Deleting the old kernels lost on your hard drive
When you update the kernel, the old version remains on the disk. If you clean up, the reward is several hundred megabytes of free disk space.
Scanning with Zenmap
Network Discovery
Discover your network with the user-friendly Zenmap network scanner.
Honeypots
Watching the Bad Guys with Cowrie
Use Cowrie as a honeypot to capture attack data and learn more about your attacker's methods.
Pretty Complex
Modern cyberwarfare and its resulting monetary allocations have significantly impacted the exploit market, but where does that lead?
Tutorials – FFmpeg
Video Wizardry
Linux has some excellent graphical video-editing tools, but sometimes working from the command line with FFmpeg is just better.
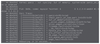
Data Harvest
Python network data visualization
The Scapy packet manipulation program lets you analyze and manipulate packets to create incident response reports or examine network security.
Keep All Your Linux Servers in Check
Front Seat
Use the browser-based Cockpit tool to monitor and administer multiple Linux servers without leaving your desk.
Contract Killer
Facebook releases its own OOM implementation
When a Linux system runs out of memory, a special agent, the out-of-memory killer, rushes to its aid. Facebook has now introduced its own OOM killer. What makes it different from its kernel-based counterpart? And what is an OOM killer really?
Wireshark
An Essential Sys Admin and Security Tool
Wireshark fills the gap between security and system administration for those who need to know more about what’s flowing through the wires or over the airwaves in the corporate network.
Subscribe to our Linux Newsletters
Find Linux and Open Source Jobs
Subscribe to our ADMIN Newsletters
Support Our Work
Linux Magazine content is made possible with support from readers like you. Please consider contributing when you’ve found an article to be beneficial.

News
-
Kali Linux Waxes Nostalgic with BackTrack Mode
For those who've used Kali Linux since its inception, the changes with the new release are sure to put a smile on your face.
-
Gnome 50 Smooths Out NVIDIA GPU Issues
Gamers rejoice, your favorite pastime just got better with Gnome 50 and NVIDIA GPUs.
-
System76 Retools Thelio Desktop
The new Thelio Mira has landed with improved performance, repairability, and front-facing ports alongside a high-quality tempered glass facade.
-
Some Linux Distros Skirt Age Verification Laws
After California introduced an age verification law recently, open source operating system developers have had to get creative with how they deal with it.
-
UN Creates Open Source Portal
In a quest to strengthen open source collaboration, the United Nations Office of Information and Communications Technology has created a new portal.
-
Latest Linux Kernel RC Contains Changes Galore
Linux kernel 7.0-rc3 includes more changes than have been made in a single release in recent history.
-
Nitrux 6.0 Now Ready to Rock Your World
The latest iteration of the Debian-based distribution includes all kinds of newness.
-
Linux Foundation Reports that Open Source Delivers Better ROI
In a report that may surprise no one in the Linux community, the Linux Foundation found that businesses are finding a 5X return on investment with open source software.
-
Keep Android Open
Google has announced that, soon, anyone looking to develop Android apps will have to first register centrally with Google.
-
Kernel 7.0 Now in Testing
Linus Torvalds has announced the first Release Candidate (RC) for the 7.x kernel is available for those who want to test it.